exe2powershell is used to convert EXE to BAT files, the previously well known tool for this was exe2bat, this is a version for modern Windows. This will convert any binary file (*.exe) to a BAT file, the resulting BAT file contains only echo commands followed by a PowerShell command to re-create the original binary file. […]
powershell
PowerMemory – Exploit Windows Credentials In Memory
PowerMemory is a PowerShell based tool to exploit Windows credentials present in files and memory, it levers Microsoft signed binaries to hack Windows. The method is totally new. It proves that it can be extremely easy to get credentials or any other information from Windows memory without needing to code in C-type languages. In addition, […]
SessionGopher – Session Extraction Tool
SessionGopher is a PowerShell Session Extraction tool that uses WMI to extract saved session information for remote access tools such as WinSCP, PuTTY, SuperPuTTY, FileZilla, and Microsoft Remote Desktop. The tool can find and decrypt saved session information for remote access tools. It has WMI functionality built in so it can be run remotely, its […]
p0wnedShell – PowerShell Runspace Post Exploitation Toolkit
p0wnedShell is an offensive PowerShell Runspace Post Exploitation host application written in C# that does not rely on powershell.exe but runs PowerShell commands and functions within a PowerShell run space environment (.NET). It has a lot of offensive PowerShell modules and binaries included making the process of Post Exploitation easier. What the author tried was […]
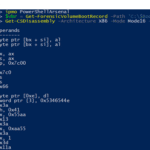
PowerShellArsenal – PowerShell For Reverse Engineering
PowerShellArsenal is basically PowerShell for reverse engineering in a module format. The module can be used to disassemble managed and unmanaged code, perform .NET malware analysis, analyse/scrape memory, parse file formats and memory structures, obtain internal system information, etc. PowerShellArsenal is comprised of the following tools: Disassembly – Disassemble native and managed code. MalwareAnalysis – […]