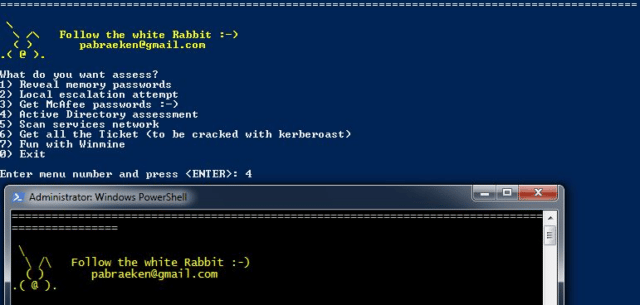
PowerMemory is a PowerShell based tool to exploit Windows credentials present in files and memory, it levers Microsoft signed binaries to hack Windows.
The method is totally new. It proves that it can be extremely easy to get credentials or any other information from Windows memory without needing to code in C-type languages. In addition, with this method, we can modify the user-land and kernel land behaviour without being caught by antivirus or new defending techniques.
It can actually be done with 4GL language-type or with a scripting language like PowerShell which is installed everywhere.
With that being said, this technique implies that the detection is made hard due to the fact that we can do pretty much what we want by sending and receiving bytes.
Features
- It’s fully written in PowerShell
- It can work locally as well as remotely
- It can get the passwords of virtual machines without having any access to them (works for Hyper-V and VMware)
- It does not use the operating system .dll to locate credentials address in memory but a Microsoft Signed Debugger
- PowerMemory maps the keys in the memory and cracks everything by itself (AES, TripleDES, DES-X)
- It breaks undocumented Microsoft DES-X
- It works even if you are on a different architecture than the target architecture
- It leaves no trace in memory
- It can manipulate memory to fool software and operating system
- It can write the memory to execute shellcode without making any API call, it only sends bytes to write at specific addresses
You can use the module waiting to be integrated to leave Wonder Land and launch a crafted advanced attack with PowerShell Empire serving as the vector.
You can download PowerMemory here:
Or read more here.
