p0wnedShell is an offensive PowerShell Runspace Post Exploitation host application written in C# that does not rely on powershell.exe but runs PowerShell commands and functions within a PowerShell run space environment (.NET). It has a lot of offensive PowerShell modules and binaries included making the process of Post Exploitation easier.
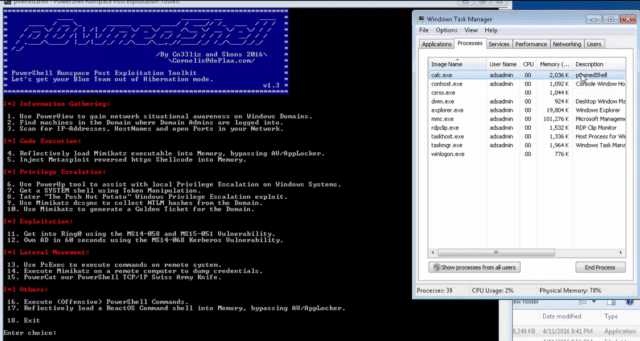
What the author tried was to build an “all in one” Post Exploitation tool which could be used to bypass all mitigations solutions (or at least some of), and that has all relevant tooling included. You can use it to perform modern attacks within Active Directory environments and create awareness within your Blue team so they can build the right defence strategies.
Features/Modules
The following PowerShell tools/functions are included:
- PowerSploit Invoke-Shellcode
- PowerSploit Invoke-ReflectivePEInjection
- PowerSploit Invoke-Mimikatz
- PowerSploit Invoke-TokenManipulation
- PowerSploit PowerUp
- PowerSploit PowerView
- HarmJ0y’s Invoke-Psexec
- Besimorhino’s PowerCat
- Nishang Invoke-PsUACme
- Nishang Invoke-Encode
- Nishang Get-PassHashes
- Nishang Invoke-CredentialsPhish
- Nishang Port-Scan
- Nishang Copy-VSS
- Kevin Robertson Invoke-Inveigh
- Kevin Robertson Tater
- FuzzySecurity Invoke-MS16-032
Powershell functions within the Runspace are loaded in memory from Base64 encode strings.
The following Binaries/tools are included:
- Benjamin DELPY’s Mimikatz
- Benjamin DELPY’s MS14-068 kekeo Exploit
- Didier Stevens modification of ReactOS Command Prompt
- MS14-058 Local SYSTEM Exploit
- hfiref0x MS15-051 Local SYSTEM Exploit
Compiling
To compile p0wnedShell you need to import this project into Microsoft Visual Studio or if you don’t have access to a Visual Studio installation, you can compile it as follows:
To Compile as x86 binary:
|
1 2 3 |
cd \Windows\Microsoft.NET\Framework\v4.0.30319 csc.exe /unsafe /reference:"C:\p0wnedShell\System.Management.Automation.dll" /reference:System.IO.Compression.dll /win32icon:C:\p0wnedShell\p0wnedShell.ico /out:C:\p0wnedShell\p0wnedShellx86.exe /platform:x86 "C:\p0wnedShell\*.cs" |
To Compile as x64 binary:
|
1 2 3 |
cd \Windows\Microsoft.NET\Framework64\v4.0.30319 csc.exe /unsafe /reference:"C:\p0wnedShell\System.Management.Automation.dll" /reference:System.IO.Compression.dll /win32icon:C:\p0wnedShell\p0wnedShell.ico /out:C:\p0wnedShell\p0wnedShellx64.exe /platform:x64 "C:\p0wnedShell\*.cs" |
p0wnedShell uses the System.Management.Automation namespace, so make sure you have the System.Management.Automation.dll within your source path when compiling outside of Visual Studio.
You can download p0wnedShell here:
Or read more here.
