So there’s been a lot of news lately about the Telegram hack and how 15 million accounts were compromised, which is not technically true. There’s 2 vectors of attack at play here, both of which regard Iranian users, but are not connected (other than the attackers probably being the same group). So the two attacks […]
Exploits/Vulnerabilities
In 2016 Your Wireless Keyboard Security Still SUCKS – KeySniffer
So you’d probably imagine that Wireless Keyboard Security is a 1998 problem and you shouldn’t even have to worry about that any more. And you’d be wrong – two-thirds of wireless keyboards, from MAJOR manufacturers are not even vaguely secure. It turns out, in 2016 when cryptography is mainstream, open-source and fairly easy to implement […]
ERTS – Exploit Reliability Testing System
ERTS or Exploit Reliability Testing System is a Python based tool to calculate the reliability of an exploit based on the number of times the exploit is able to control EIP register with the desired address/value. It’s created to help you code reliable exploits and take the manual parts out of running and re-running exploits […]
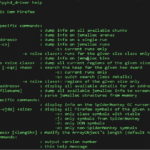
shadow – Firefox Heap Exploitation Tool (jemalloc)
shadow is a new, extended (and renamed version) of a Firefox heap exploitation tool, which is quite a swiss army knife for Firefox/jemalloc heap exploitation. If you want to dive in really deep to this tool, and the technicalities behind it check this out – OR’LYEH? The Shadow over Firefox [PDF] Support shadow has been […]
Intel Hidden Management Engine – x86 Security Risk?
So it seems the latest generation of Intel x86 CPUs have implemented a Intel hidden management engine that cannot be audited or examined. We can also assume at some point it will be compromised and security researchers are labelling this as a Ring -3 level vulnerability. This isn’t a new issue though, people have been […]