Binwalk is a fast and easy to use Python-based firmware security analysis tool that allows for firmware analysis, reverse engineering, and extraction of firmware images.
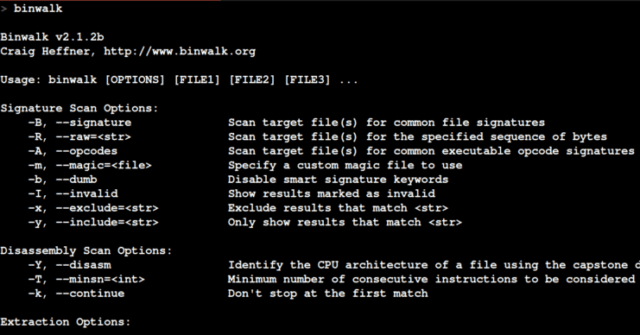
Features of Binwalk Firmware Security Analysis & Extraction Tool
- Scanning Firmware – Binwalk can scan a firmware image for many different embedded file types and file systems
- File Extraction – You can tell binwalk to extract any files that it finds in the firmware image
- Entropy Analysis – Can help identify interesting sections of data inside a firmware image
- String Search – Allows you to search the specified file(s) for a custom string
There are also various filters such as by CPU architecture, number of instructions, include filter, exclude filter,
Installation of Binwalk Firmware Security Analysis & Extraction Tool
Download binwalk:
|
1 2 |
$ wget https://github.com/ReFirmLabs/binwalk/archive/master.zip $ unzip master.zip |
Install binwalk; if you have a previously installed version of binwalk, it is suggested that you uninstall it before upgrading:
|
1 |
$ (cd binwalk-master && sudo python setup.py uninstall && sudo python setup.py install) |
Debian users can install all optional and suggested extractors/dependencies using the included deps.sh script (recommended):
|
1 |
$ sudo ./binwalk-master/deps.sh |
If you are not a Debian user, or if you wish to install only selected dependencies, see the INSTALL documentation for more details.
Usage of Binwalk Firmware Security Analysis & Extraction Tool
File Extraction
You can tell binwalk to extract any files that it finds in the firmware image with the -e option:
|
1 |
$ binwalk -e firmware.bin |
Binwalk will even recursively scan files as it extracts them if you also specify the -M option:
|
1 |
$ binwalk -Me firmware.bin |
And if the -r option is specified, any file signatures that couldn’t be extracted – or that resulted in 0-size files – will be automatically deleted:
|
1 |
$ binwalk -Mre firmware.bin |
To extract one specific signature type, specify one or more -D type options:
|
1 |
$ binwalk -D 'png image:png' firmware.bin |
Entropy Analysis
What happens if binwalk doesn’t report any signatures? Or, how do you know binwalk didn’t miss anything interesting?
Entropy analysis can help identify interesting sections of data inside a firmware image:
|
1 |
$ binwalk -E firmware.bin |
You can download Binwalk here:
Or read more here.

steve says
Binwalk is a tool that tool for cyber security for sure.