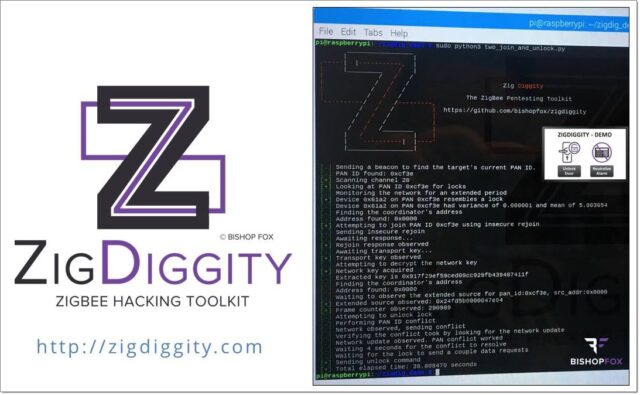
ZigDiggity a ZigBee Hacking Toolkit is a Python-based IoT (Internet of Things) penetration testing framework targeting the ZigBee smart home protocol.
ZigBee continues to grow in popularity as a method for providing simple wireless communication between devices (i.e. low power/traffic, short distance), & can be found in a variety of consumer products that range from smart home automation to healthcare. Security concerns introduced by these systems are just as diverse and plentiful, underscoring a need for quality assessment tools.
This ZigBee penetration testing framework enables cybersecurity professionals, auditors, and developers to run complex interactions with ZigBee networks using a single device.
The current version of ZigDiggity is solely designed for use with the Raspbee, the RaspBee premium is ZigBee addon for Raspberry Pi with Firmware.
The RaspBee provides:
- Pluggable add on with radio module (IEEE 802.15.4) for Raspberry Pi
- Brings Raspberry Pi as LAN-ZigBee gateway
- Frequency: 2.4 GHz ISM band, can be used worldwide
- Based on Atmel´s single chip microcontroller ATmega256RFR2
- With ZigBee firmware and extensive software package to control up to 200 devices
Using ZigDiggity the ZigBee Hacking Toolkit
Currently, scripts are available in the root of the repository, they can all be run using Python3:
|
1 |
python3 listen.py -c 15 |
When running with Wireshark, root privileges may be required.
Scripts for ZigBee Hacking
- ack_attack.py – Performs the acknowledge attack against a given network.
- beacon.py – Sends a single beacon and listens for a short time. Intended for finding which networks are near you.
- find_locks.py – Examines the network traffic on a channel to determine if device behavior looks like a lock. Displays which devices it thinks are locks.
- insecure_rejoin.py – Runs an insecure rejoin attempt on the target network.
- listen.py – Listens on a channel piping all output to wireshark for viewing.
- scan.py – Moves between channels listening and piping the data to wireshark for viewing.
- unlock.py – Attempts to unlock a target lock
You can download ZigDiggity here:
Or read more here.

ida says
how do i download this thing
ibb says
how will i download this software
Darknet says
There’s literally a link to download it at the bottom of the post, what more do you want?
ipeed says
How about singing Never Gonna Give You Up?