snallygaster is a Python-based tool that can help you to scan for secret files on HTTP servers, files that are accessible that shouldn’t be public and can pose a security risk.
Typical examples include publicly accessible git repositories, backup files potentially containing passwords or database dumps. In addition it contains a few checks for other security vulnerabilities.
snallygaster HTTP Secret File Scanner Features
This is an overview of the tests provided by snallygaster.
- lfm_php – Checks for Lazy File Manager
- idea – Config file for JetBrains
- symphony_databases_yml – Symphony database config file
- rails_database_yml – Ruby on Rails default config file
- git_dir – Download the full Git repo
- svn_dir – Download the full SVN repo
- cvs_dir – Download the full CVS repo
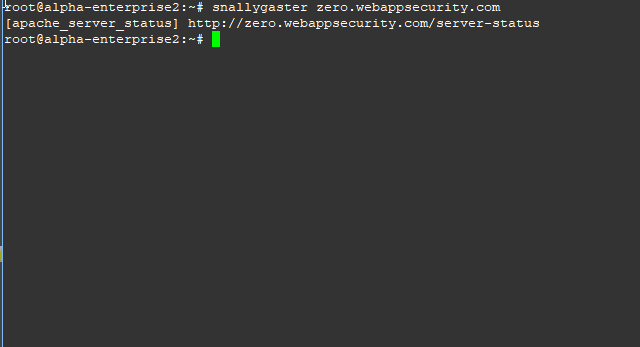
- apache_server_status – Apache server-status page
- coredump – Memory dump file on Linux
- sftp_config – Configuration file from sublime FTP client
- wsftp_ini – Configuration file for WS_FTP
- filezilla_xml – Configuration file for FileZilla
- winscp_ini – Configuration file for WinSCP
- ds_store – Apple OS X File Manager
- backupfiles – Backup files and other leftovers from editors
- deadjoe – JOE editor dump file
- sql_dump – Checks for common names of SQL database dumps
- bitcoin_wallet – Scans for Bitcoin wallet files
- drupal_backup_migrate – Drupal migration backup
- magento_config – Magento XML based config file
- xaa – Output of the Linux split command
- optionsbleed – Checks for Optionsbleed vuln
- privatekey – Checks for private keys
- sshkey – Looks for SSH private keys
- dotenv – Looks for Laravel .env files
- invalidsrc – Checks webpage source for all inaccessible references
- ilias_defaultpw – Checks for the Ilias e-learning software default creds
- cgiecho – Leaks files from cgiemail
- phpunit_eval – Test for remote code execution
- axfr – Checks for DNS AXFR zone transfer requests
You could probably achieve something similar with Burp Intruder or Patator and something like the quickhits list from SecLists.
You can download snallygaster here:
Or read more here.
