I love the Burp Suite, I really do. It’s pretty much my favourite local proxy program and my favourite suite of tools for security testing web applications (especially the session investigation and manipulation parts).
Another great thing is it’s cross platform, so you don’t have to learn different tools for Windows and Linux.
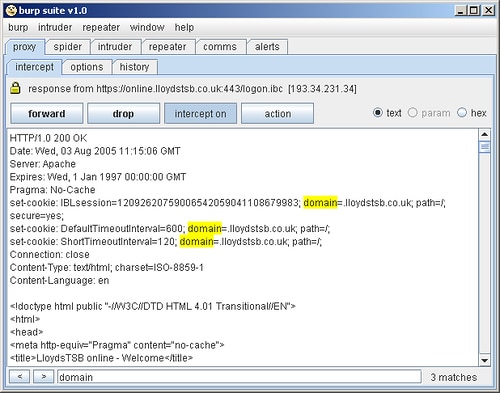
Basically Burp suite is an integrated platform for attacking web applications. It contains all of the burp tools (proxy, spider, intruder and repeater) with numerous interfaces between them designed to facilitate and speed up the process of attacking a web application. All plugins share the same robust framework for handling HTTP requests, authentication, downstream proxies, logging, alerting and extensibility.
Burp suite allows an attacker to combine manual and automated techniques to enumerate, analyse, attack and exploit web applications. The various burp tools work together effectively to share information and allow findings identified within one tool to form the basis of an attack using another.
Key features unique to burp suite include:
- Ability to “passively” spider an application in a non-intrusive manner, with all requests originating from the user’s browser.
- One-click transfer of interesting requests between plugins, e.g. from the proxy request history, or a web page form enumerated with burp spider.
- Extensibility via the IBurpExtender interface, which allows third-party code to extend the functionality of burp suite. Data processed by one plugin can be used in arbitrary ways to affect the behaviour and results of other plugins.
- Centrally configured settings for downstream proxies, web and proxy authentication, and logging.
- Plugins can run in a single tabbed window, or be detached in individual windows.
- All plugin and suite configuration is optionally persistent across program loads.
- Runs in both Linux and Windows.
I’ll try and do some tutorials for Burp later on and perhaps I’ll focus a bit more on Burp Proxy alone, as it’s an extremely powerful tool.
Burp suite is a Java application, and runs on any platform for which a Java Runtime Environment is available. It requires version 1.4 or later. The JRE can be obtained for free from Sun.
You can download Burp Suite below, both archives contain the same files, which will run under both Windows and Linux.
