So far this Nayana payout is the biggest ransomware payment I’ve seen reported, there’s probably some bigger ones been paid but kept undercover.
Certainly a good deal for the bad actors in this play, and well using an outdated Kernel along with PHP and Apache versions from 2006 you can’t feel too sorry for Nayana.
A South Korean web hosting company is forking out just over US$1 million to ransomware scum after suffering more than eight days of nightmare.
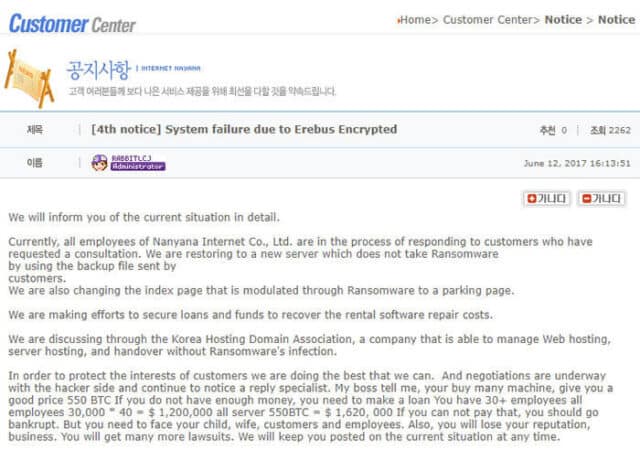
Nayana first announced the attack on June 10, saying customer video files and its database had been encrypted, and promising to work to recover the data.
More than 150 servers were hit, hosting the sites of more than 3,400 mostly small business customers.
After a lengthy negotiation with the hackers, a demand for Bitcoin worth 5 billion won (nearly $4.4 million) was trimmed to around $1 million (397.6 Bitcoin), and the company paid up. The ransom was demanded in three instalments; so far, two have been made.
They’ve made 11 Announcements so far about the situation with the latest being from yesterday, in which they state they’ve paid the ransom but it will still quite some time for them to decrypt the customer data and restore it properly (10 days or more in some cases).
Obviously it’ll depend on the number of files, the size of the files encrypted and the power of the machine running the decryption.
Trend Micro reckons the attack used a version of Erebus ported to Linux.
Trend says at the time of the attack, Nayana was running a witch’s brew of vulnerable systems – an old Linux kernel (2.6.24.2) compiled in 2008, Apache 1.3.36 and PHP 5.1.4 (both dating from 2006).
As well as getting schooled in why systems need to be kept up to date, Nayana says it’s working with the Korea Internet and Security Agency and other “cyber criminal investigators”.
The company’s next recovery status announcement is due today (Tuesday, 20 June).
For those that say they don’t have a budget for security, they should look at this. You could hire a whole red team, an external security audit and use top notch protection tools for far less than $1 Million USD.
I hope this serves as a lesson to more organisations than just Nayana.
Source: The Register
