It’s not the first time Shadow Brokers has been on the radar with NSA Hacking Tools, in August 2016 they exposed a bunch of 0-day exploits (also from 2013).
This cache of tools appears to be from 2013, so was probably snatched during the same intrusion. This is somewhat more dangerous though as it provides what are essentially point-and-click tools for exploiting all types of Microsoft systems.
The Shadow Brokers have leaked more hacking tools stolen from the NSA’s Equation Group – this time four-year-old exploits that attempt to hijack venerable Windows systems, from Windows 2000 up to Server 2012 and Windows 7 and 8.
The toolkit puts into anyone’s hands – from moronic script kiddies to hardened crims – highly classified nation-state-level weaponry that can potentially compromise and commandeer systems around the world. This is the same powerful toolkit Uncle Sam used once upon a time to hack into and secretly snoop on foreign governments, telcos, banks, and other organizations.
The files range from Microsoft Windows exploits to tools for monitoring SWIFT interbank payments. Ongoing analysis of the leaked documents and executables has revealed Cisco firewalls and VPN gateways are also targets.
The Shadow Brokers tried auctioning off the stolen cyber-weapons to the highest bidder, but when that sale flopped with no buyers, the team started releasing the gear online for free anyway.
“The shadow brokers not wanting going there. Is being too bad nobody deciding to be paying the shadow brokers for just to shutup and going away,” the group said in a typically garbled blog post.
Just exploits take a little more skill to use, but these tools allow the most n00b skiddies to carry out some pretty devastating attacks on machines running Win2k all the way to Windows 8 and Windows Server.
It seems like they tried to auction of this kit and got the cold shoulder, which should be expected as those with serious money are not gonna drop it on a bunch of 2013 software.
“The Shadow Brokers rather being getting drunk with McAfee on desert island with hot babes. Maybe if all suviving WWIII the shadow brokers be seeing you next week. Who knows what we having next time?”
For IT managers and normal folks, the Windows-hacking arsenal, which dates to around mid-2013, is the most concerning. It contains exploits for vulnerabilities that can be used to hack into unpatched Windows systems, from Windows 2000 to Windows 8 and Server 2012. In some cases this can be done across the network or internet via SMB, RDP, IMAP, and possibly other protocols.
If you have a vulnerable aging machine with those services running, it is possible they can be hijacked using today’s dumped tools – if not by strangers on the ‘net then potentially by malicious employees or malware already on your network. If you’re running the latest up-to-date gear, such as Windows 10, none of this will directly affect you – but not everyone is so lucky. There are plenty of organizations out there that cannot keep every box up to date, for various reasons.
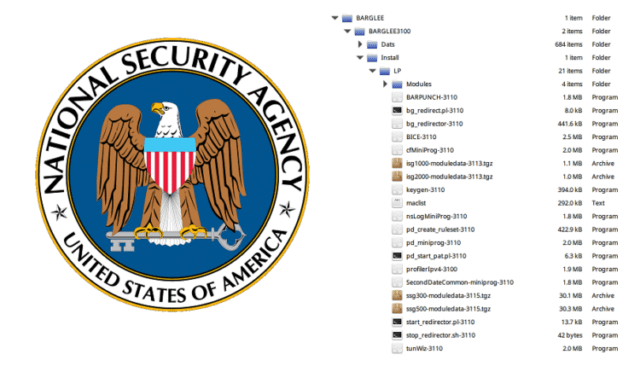
The leaked archive also contains the NSA’s equivalent of the Metasploit hacking toolkit: FUZZBUNCH.
Matthew Hickey, cofounder of British security shop Hacker House, told The Register FUZZBUNCH is a very well-developed package that allows servers to be penetrated with a few strokes of the keyboard. The toolkit has modules to install a backdoor on invaded boxes to remote control the gear and romp through file systems.
Some part of me is glad to see the NSA software appears to be well written and well architected, at least they are doing well on those fronts. Plus 4 years later I’d imagine the malicious software capabilities they have are much more powerful.
We will have to wait and see if any more comes from this.
Source: The Register

mithrandir says
So where are the tools??
Lucas says
Have you already found them online?
applejacks says
Hello, I noticed what may be a spelling/typo error… “This cache of tools appears to be from 2013, so was properly snatched during the same intrusion.”
Darknet says
Thanks,fixed!