It seems malware writers using exclusion lists is not something new, but it’s still concerning people. To me it’d be a pretty obvious avenue, especially if you were crafting something a little more nefarious than average – like APT malware (Advanced Persistent Threat) tools.
Definitely a chicken and egg problem, especially with Windows if you don’t exclude the OS and a bunch of system directories (including loads of ‘known’ software) you will have endless false positives. But then in this case, it can be abused.
Advanced malware writers are using anti-virus exclusion lists to better target victims, researchers say.
Software vendors use exclusion lists to explain the files and directories that antivirus software should ignore to avoid false positives and ensure an application’s proper operations.
Such lists are common: Citrix published one last week while it doesn’t take much Googling to find more. For example, here’s one from SolarWinds, and a few more from VMware, Microsoft, SAP, CA , Veritas and Sage.
When Citrix’s list emerged, The Reg pondered the lists’ possible use as a handy guide to the process names and directory locations hackers could target to take down users. Once you know, for example, that thisprocess.exe is whitelisted, creating an attack that runs as thisprocess.exe looks like an obvious tactic.
We were right: an independent malware researcher who prefers to be known as by his hacker handle “UnixFreakxjp” says some advanced malware writers are exploiting these published exclusions to produce malware targeted to particular enterprises.
“There are malware writers using whitelisted exclusion files, mostly APT (advanced persistent threat) and targeted infection groups rather than public malware operators,” he says.
The exclusion lists are actually really handy documents for malware authors as they even give executable names which are whitelisted to run. Plus directories that are exempt for scanning where you can stash your dodgy binaries.
It’s not like Windows needs more information out there on how to make it less secure..
He says the file exclusions are necessary to mitigate the “annoying” false positives caused by antivirus platforms, adding that many businesses are impacted by the erroneous flags.
Exclusions are, however, a band-aid fix and do not address core malware diagnosis problems.
Another respected security researcher requesting anonymity says he has not seen malware targeting exclusion lists but imagines it would be useful to advanced attackers.
He says the Locky ransomware actors, who tend to compromise corporates over individuals, could use a vendor’s recommended antivirus exclusion list to target clients.
“It would be interesting for attackers who know their victim is indeed using Citrix,” he says. Or known to be using any other exclusion-list-using vendor.
“The [exclusion] paths could be a nice place to store malware payloads before execution.”
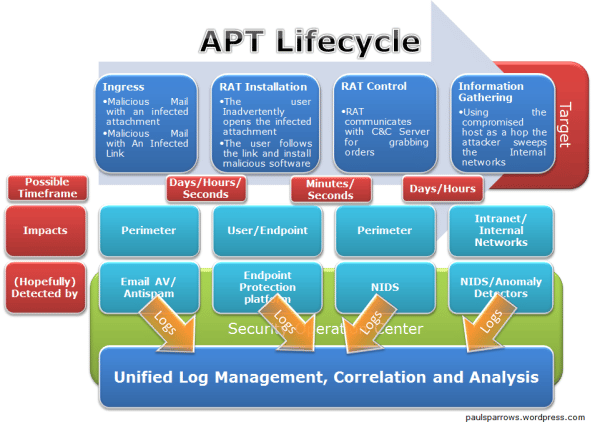
He notes that organisations should have multi-layered defences and not rely solely on antivirus.
I don’t think most common garden malware floating around the web will use these kind of techniques, plus the average computer wont have software like Citrix installed on it anyway – but for corporates it’s something to be aware of.
And as mentioned above, and always, security is best treated with an onion approach of many layers (including security through obscurity) – so be on guard.
Source: The Register

Nick says
Why exclude by name instead of just excluding signed executables or those that have a certain hash?
Darknet says
Hash would require a lot of updates by AV vendors I guess, with so many exclusions, hash would change every time the software was updated/patched. And bad stuff has been signed before..