dnsteal is a DNS exfiltration tool, essentially a fake DNS server that allows you to stealthily extract files from a victim machine through DNS requests.
dnsteal is coded in Python and is available on Github.
Features
dnsteal currently has:
- Support for multiple files
- Gzip compression supported
- Supports the customisation of subdomains
- Customise bytes per subdomain and the length of filename
Usage
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 |
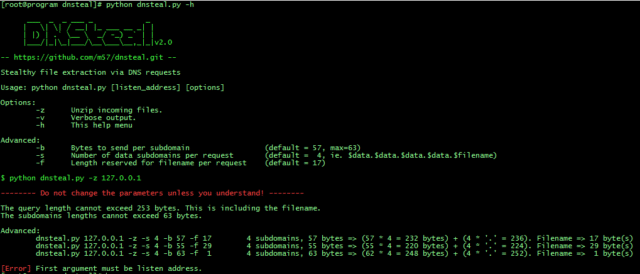
# cd dnsteal/ # ./dnsteal.py -h ___ _ _ ___ _ _ | \| \| / __| |_ ___ __ _| | | |) | .` \__ \ _/ -_) _` | | |___/|_|\_|___/\__\___\__,_|_|v2.0 -- https://github.com/m57/dnsteal.git -- Stealthy file extraction via DNS requests Usage: python ./dnsteal.py [listen_address] [options] Options: -z Unzip incoming files. -v Verbose output. -h This help menu Advanced: -b Bytes to send per subdomain (default = 57, max=63) -s Number of data subdomains per request (default = 4, ie. $data.$data.$data.$data.$filename) -f Length reserved for filename per request (default = 17) $ python ./dnsteal.py -z 127.0.0.1 -------- Do not change the parameters unless you understand! -------- The query length cannot exceed 253 bytes. This is including the filename. The subdomains lengths cannot exceed 63 bytes. Advanced: ./dnsteal.py 127.0.0.1 -z -s 4 -b 57 -f 17 4 subdomains, 57 bytes => (57 * 4 = 232 bytes) + (4 * '.' = 236). Filename => 17 byte(s) ./dnsteal.py 127.0.0.1 -z -s 4 -b 55 -f 29 4 subdomains, 55 bytes => (55 * 4 = 220 bytes) + (4 * '.' = 224). Filename => 29 byte(s) ./dnsteal.py 127.0.0.1 -z -s 4 -b 63 -f 1 4 subdomains, 63 bytes => (62 * 4 = 248 bytes) + (4 * '.' = 252). Filename => 1 byte(s) # |
You can download dnsteal here:
Or read more here.
