Zenmap download below, this is the official cross-platform Nmap GUI. It is a multi-platform (Linux, Windows, Mac OS X, BSD, etc.) free and open source application which aims to make Nmap easy for beginners to use while providing advanced features for experienced Nmap users.
No frontend can replace good old command-line Nmap. The nature of a frontend is that it depends on another tool to do its job. Therefore the purpose of Zenmap is not to replace Nmap, but to make Nmap more useful. Here are some of the advantages Zenmap offers over plain Nmap.
Zenmap Nmap GUI Purpose
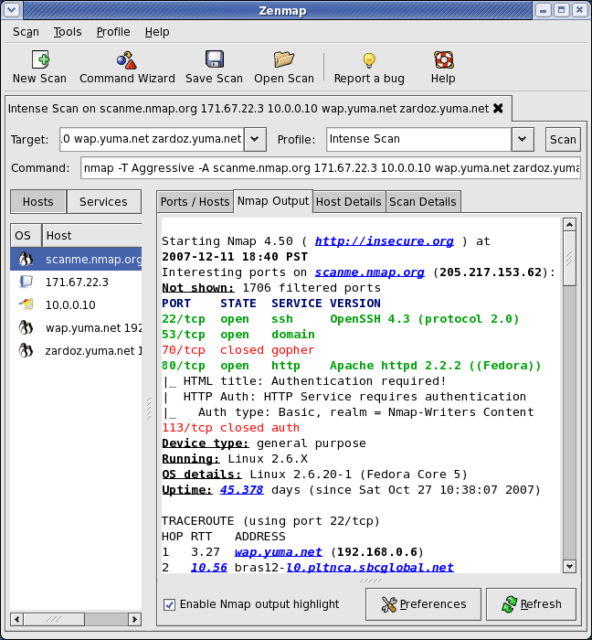
- Interactive and graphical results viewing – In addition to showing Nmap’s normal output, Zenmap can arrange its display to show all ports on a host or all hosts running a particular service. It summarizes details about a single host or a complete scan in a convenient display. Zenmap can even draw a topology map of discovered networks. The results of several scans may be combined together and viewed at once.
- Comparison – Zenmap has the ability to show the differences between two scans. You can see what changed between the same scan run on different days, between scans of two different hosts, between scans of the same hosts with different options, or any other combination. This allows administrators to easily track new hosts or services appearing on their networks, or existing ones going down.
- Convenience – Zenmap keeps track of your scan results until you choose to throw them away. That means you can run a scan, see the results, and then decide whether to save them to a file. There is no need to think of a file name in advance.
- Repeatability – Zenmap’s command profiles make it easy to run the exact same scan more than once. There’s no need to set up a shell script to do a common scan.
- Discoverability – Nmap has literally hundreds of options, which can be daunting for beginners. Zenmap’s interface is designed to always show the command that will be run, whether it comes from a profile or was built up by choosing options from a menu. This helps beginners learn and understand what they are doing. It also helps experts double-check exactly what will be run before they press “Scan”.
Zen Map Nmap GUI Features
- Frequently used scans can be saved as profiles to make them easy to run repeatedly.
- A command creator allows interactive creation of Nmap command lines.
- Scan results can be saved and viewed later.
- Saved scan results can be compared with one another to see how they differ.
- The results of recent scans are stored in a searchable database.
Zenmap Download for Windows & OSX
Zenmap OSX and Zenmap Windows are already included in the installer and the source, so you can download it using that:
– Windows: nmap-7.60-setup.exe
– Mac OSX: nmap-7.60.dmg
– Source: nmap-7.60.tar.bz2
Or read more here.
