[ad]
At last a new major release of Nmap!
If for some odd reason you don’t already know what Nmap is, it is a free and open source utility for network exploration or security auditing. Many systems and network administrators also find it useful for tasks such as network inventory, managing service upgrade schedules, and monitoring host or service uptime. Nmap uses raw IP packets in novel ways to determine what hosts are available on the network, what services (application name and version) those hosts are offering, what operating systems (and OS versions) they are running, what type of packet filters/firewalls are in use, and dozens of other characteristics.
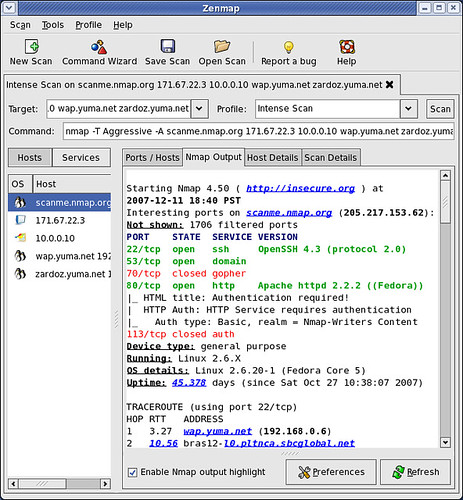
The changelog shows 320 changes since 4.00 with a lot of great stuff in this release! It has a brand new GUI and results viewer (Zenmap), a scripting engine allowing you to write your own scripts for high-performance network discovery (or use one of the 40 scripts shipped with it), the 2nd generation OS detection system (now with more than a thousand fingerprints), nearly 1,500 more version detection signatures, and a lot more!
Zenmap is the official Nmap Security Scanner GUI. It is a multi-platform (Linux, Windows, Mac OS X, BSD, etc.) free and open source application which aims to make Nmap easy for beginners to use while providing advanced features for experienced Nmap users. Frequently used scans can be saved as profiles to make them easy to run repeatedly. A command creator allows interactive creation of Nmap command lines. Scan results can be saved and viewed later. Saved scan results can be compared with one another to see how they differ. The results of recent scans are stored in a searchable database.
More on Zenmap here:
You can download the new Nmap here:
Or read more here.

net2004eng says
I just installed the new version 4.50 from insecure.org. Zenmap – the graphical front end, like Darknet mentions, I find eerily similar to UMIT. Primae facie I found nothing different between the 2!
Sir Henry says
Although I have always been a cli-only nmap user, I would be intrigued to see how things are with the GUI, as well as the changes in the newest version.
net2004eng says
@SirHenry
I am a Nmap CLI kind of guy too, but when I have taught Nmap tutorials to fellow security engineers, I have liked to include UMIT in the lesson. Reason is, for those who are not particulary fond of the CLI UMIT/Zenmap are great for those just learning the tool. On the bottom of the GUI, it prints out the CLI equalivent of what you are doing in the GUI – which can even be helpful for those familiar with the scanner already…very nice indeed!
Sir Henry says
I think that adding the cli equivalent is a brilliant move on their part. If only Cisco would do that with their L2/L3 devices. I will have to compile the latest version and try it out.
Pantagruel says
Indeed a good thing to include a GUI, even though most will persist in using the CLI (I still preffer an remote SSH CLI over X being tunneled through ssh because of speed reasons) the GUI is a nice way to show others what to do with nmap.
Sir Henry says
I have to say, my initial testing with the latest version leaves me with a smile on my face. I definitely agree with the lot of you about teaching people the use of nmap and how this can assist with getting someone familiar with it. I can see extreme value in the command constructor for the latter purpose, as well.
cpj says
On using the interface, I must say that it is very helpful for someone learning to use the program to its full potential. When I first used UMIT, I had never used and frankly ignored some of the triggers that appear in the commands. Now I suppose those who do not know about UMIT will get an interface with their Nmap, and this might generally be helpful.
I’m fairly new to Nmap, but at least I discovered which (unnecessary) services were leaving open ports on some of our systems.
goodpeople says
Nmap rocks! The gui will only make it more popular. Up til now my studens were somewhat reluctant to start using nmap, but this will definately take their reservation away!
Sir Henry says
@goodpeople:
Is it that they simply do not see the need or do not feel comfortable with the cli?
eM3rC says
Like everyone above me says, EXCELLENT PROGRAM!
-gah this anti-bot addon to the posting box doesn’t work 1/2 the time =\-
razta says
Old post I know… has any one tried Angry IP Scanner v3 beta? Great tool, and now v3 is cross platform! Loads of new options in v3, great GUI and fast scanning! You should give it a try: http://www.angryziber.com
austin says
good