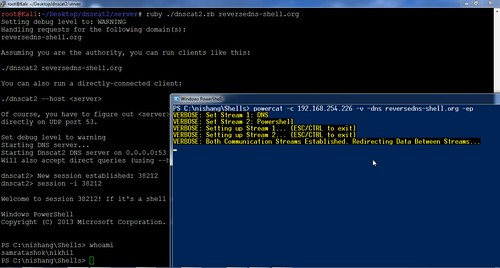
This DNS tunnel tool named dnscat2 creates an encrypted tunnel over the DNS protocol primarily as a command-and-control (C&C) channel for penetration testers as outbound DNS is rarely blocked in networks.
This makes it a very effective tunnel out of almost every network.
Overview
dnscat2 comes in two parts: the client and the server.
The client is designed to be run on a compromised machine. It’s written in C and has the minimum possible dependencies. It should run just about anywhere (if you find a system where it doesn’t compile or run, please file a ticket, particularly if you can help me get access to said system).
When you run the client, you typically specify a domain name. All requests will be sent to the local DNS server, which are then redirected to the authoritative DNS server for that domain (which you, presumably, have control of).
If you don’t have an authoritative DNS server, you can also use direct connections on UDP/53 (or whatever you choose). They’ll be faster, and still look like DNS traffic to the casual viewer, but it’s much more obvious in a packet log (all domains are prefixed with “dnscat.”, unless you hack the source). This mode will frequently be blocked by firewalls.
The server is designed to be run on an authoritative DNS server. It’s in ruby, and depends on several different gems. When you run it, much like the client, you specify which domain(s) it should listen for in addition to listening for messages sent directly to it on UDP/53. When it receives traffic for one of those domains, it attempts to establish a logical connection. If it receives other traffic, it ignores it by default, but can also forward it upstream.
How is it different from…
dnscat2 strives to be different from other DNS tunnelling protocols by being designed for a special purpose: command and control.
This isn’t designed to get you off a hotel network, or to get free Internet on a plane. And it doesn’t just tunnel TCP.
It can tunnel any data, with no protocol attached. Which means it can upload and download files, it can run a shell, and it can do those things well. It can also potentially tunnel TCP, but that’s only going to be added in the context of a pen-testing tool (that is, tunnelling TCP into a network), not as a general purpose tunnelling tool. That’s been done, it’s not interesting (to me).
It’s also encrypted by default. I don’t believe any other public DNS tunnel encrypts all traffic!
You can download dnscat2 here:
Win32 Client – dnscat2-v0.05-client-win32.zip
Linux x86 Client – dnscat2-v0.05-client-x86.tar.bz2
Linux x64 Client – dnscat2-v0.05-client-x64.tar.bz2
Server – dnscat2-v0.05-server.zip
Or read more here.
