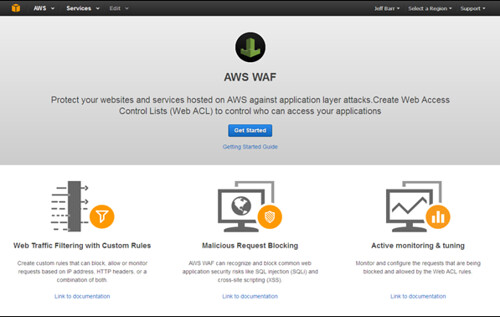
So Amazon is stepping up its security game again, this time with an AWS Web Application Firewall or WAF as they are commonly known. Generally a WAF is designed to protect you against common web threats such as XSS (Cross Site Scripting), SQL Injection, and other common patterns (LFI, RFI etc).
We have written about one such tool before: Shadow Daemon – Web Application Firewall and now modern versions of nginx come with an option to use naxsi out of the box. Plus the most famous one of all of course, ModSecurity.
As with everything AWS related, it seems rather complex to use, and for every rule you want to add, you have to pay more..so of course – it’s costly.
AWS WAF, launched on the first day of Amazon’s AWS re:Invent 2015 conference, is designed to give users control over the type of traffic that is allowed or not allowed to reach their web applications. By defining Access Control Lists (ACLs), rules, and actions, users can block SQL injection, cross-site scripting (XSS) and other common attack patterns. Rules can also be created for each user’s specific application.
The new security product also includes a full-featured API that can be used to automate the creation, deployment and maintenance of rules.
Jeff Barr, chief evangelist for Amazon Web Services, published a blog post detailing the various AWS WAF concepts, including conditions, rules, web ACLs, and actions.
Barr explained that conditions are designed for inspecting incoming requests. They can analyze the incoming IP address and various parameters of the request, such as URI, query string, HTTP header, and HTTP method.
Rules rely on these conditions to block or allow certain types of requests, while actions dictate the action that is taken when a request matches the conditions in a rule. ACLs reference one or more of these rules and the action that is taken for each of them.
It’s certainly a step in the right direction though, and I’m glad to see Amazon making security easier for people. The more Security as a Service offerings cloud providers have available, the more secure the average web app will become.
Well, that is also depending on a big IF, IF people are willing to pay for such services. I’m sure larger companies already have their own rolled solutions in place, but this might be a great fit for medium sized organizations
The Amazon post about it can be found here: New – AWS WAF
Before the rules and filters are deployed, users need to identify the Amazon CloudFront distribution they want to protect with AWS WAF.
Understanding these concepts is important for calculating the costs of running the service. According to Amazon, there are no minimum charges and pricing is calculated based on the number of defined ACLs and the number of rules deployed for them.
The charge for each ACL is $5 per month, and the charge per rule per ACL per month is $1. The volume of web requests handled by AWS WAF is also charged by Amazon, with $0.60 for every million requests. Amazon has pointed out that there are no additional charges for reusing an ACL across multiple CloudFront distributions.
AWS WAF is not the only security product offered by Amazon to AWS customers. At last year’s re:Invent conference, the company launched three new enterprise security and governance solutions for AWS. In June, Amazon released a new open source implementation of the TLS protocol that the company plans on integrating into several AWS services.
It’ll be interesting to see what the adoption of this is like, we’ll have to wait a couple of weeks I guess before people start writing about the on real World usage (difficulties, effectiveness, cost etc).
I know everyone builds everything on Amazon, so it shouldn’t be long. Apart from me, I’m a weirdo..I use Linode and Digital Ocean.
Source: Security Week

Zak Siddiqui says
Unfortunately whilst it block SQL Injection, it doesn’t have rules for CSRF and XSS protection.
(At least not at time of writing)
Darknet says
Well it’s basically a regex rules engine, it may only provide SQL Injection based rules by default but it can protect against the others with your own rules.