The peinjector is a MITM PE file injector, the tool provides different ways to infect Windows platform executable files (PE COFF) with custom payloads without changing the original functionality. It creates patches, which are then applied seamlessly during file transfer. It is very performant, lightweight, modular and can be operated on embedded hardware.
Features
- Full x86 and x64 PE file support.
- Open Source
- Fully working on Windows and Linux, including automated installation scripts.
- Can be operated on embedded hardware, tested on a Raspberry Pi 2.
- On Linux, all servers will be automatically integrated as service, no manual configuration required.
- Plain C, no external libraries required (peinjector).
- MITM integration is available in C, Python and Java. A sample Python MITM implementation is included.
- Foolproof, mobile-ready web interface. Anyone who can configure a home router can configure the injector server.
- Easy to use integrated shellcode factory, including reverse shells, or meterpreter.
How it Works
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 |
+ configuration | payload | ... +-----------v------------+ +-------+ | | | PATCH <-------+ libpeinfect <--+ +-------+ | | | +-----------+------------+ | | | +-----------v------------+ | | | | +---------------> libpetool | | | change values | | | | add sections +-----------^------------+ | | resize sect. | | + ... +----v----+ | | PEFILE +----------+ +----^----+ | +-----------v------------+ PE File data | | PE File data +---------------> libpefile +---------------> | | +------------------------+ |
peinjector contains the following:
- libpefile – Provides PE file parsing, modification and reassembling capabilities, based on PE COFF specification. Also works with many non-compliant and deliberately malformed files which the Windows Loader accepts.
- libpetool – Provides more complex modifications (adding/resizing sections). Keeps header values PE COFF compliant.
- libpeinfect – Provides different infection methods, removes integrity checks, certificates, etc. It can fully infect a file (statically, e.g. from disk) or generate a patch (for MITM infection. Connectors which work with these patches are available in C, Python and Java). The infected file keeps its original functionality.
Servers
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 |
+-----------------+-+ | web browser |X| +-------------+ +-----------------+-+ | peinjector- | | _____ | ------->+ interceptor +---------> | / \ | -orig.->+ (MITM) +-patched-> | | () () | | -data-->+ +-data----> | \ ^ / | ------->+ +---------+ +---------> | ||||| | | |connector| | | | +-+-+-----^-+-+ +-----+------^------+ raw | | send | | get header | | patch config | | status | | | | +-+-v-----+-+-+ +-+---v------+---+-+ | |data port| | | |http(s) server| | | +---------+ | | +--------------+ | | peinjector | | | | (core +---+ crtl +---+ peinjector- | | engine) |c p| protocol |c p| control | | |r o+----------->r r| (user | | |t r<-----------+t o| interface) | | |l t| |l .| | +---------+---+ +---+--------------+ |
- peinjector – Provides PE file patching as a service. Just send the raw header of your PE file and you’ll receive a custom-made patch for it. Can be remotely controlled via a command protocol.
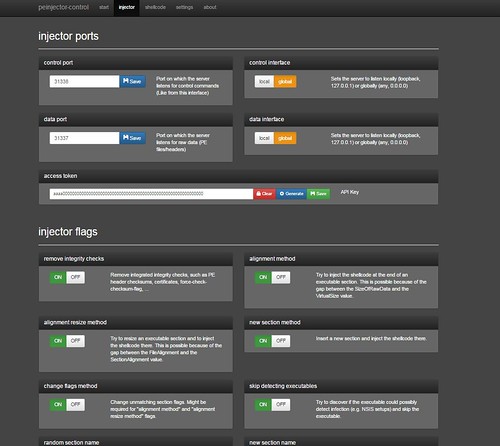
- peinjector-control – Web interface to configure and control a peinjector server. A small shellcode factory with some basic shellcodes, automatic encryptoin/obfuscation and thread generation is provided – alternatively, custom shellcode can be injected.
- peinjector-interceptor – Sample MITM integration. Based on Python and libmproxy, supports SSL interception, can act as transparent Proxy, HTTP Proxy, … . Provides seamless PE patching capabilities.
You can download peinjector here:
Or read more here.

LOL says
“rasperberry”???? LOL!!!
Darknet says
Oops..