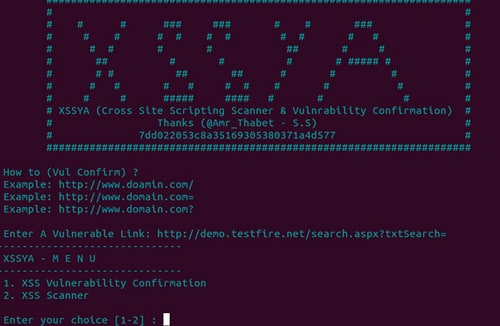
We first published about XSSYA back in 2014, and it seemed to be pretty popular, there’s not a whole lot of tools in the XSS (Cross Site Scripting) space.
For those who are unfamiliar, XSSYA used to be Cross Site Scripting aka XSS Vulnerability Scanner & Confirmation tool – the scanning portion has been removed to reduce false positives and it now focuses on XSS Vulnerability Confirmation.
It uses two main methods:
- Method number 1 for Confirmation Request and Response
- Method number 2 for Confirmation Execute encoded payload and search for the same payload in web HTML code but decoded
We have written about a couple of XSS related tools before:
– XSS-Proxy – Cross Site Scripting Attack Tool
– XSS Shell v0.3.9 – Cross Site Scripting Backdoor Tool
Features
- Supports HTTPS
- After Confirmation (execute payload to get cookies)
- Identify 3 Types of WAF (Mod_Security – WebKnight – F5 BIG IP)
- Can be run in Windows & Linux
- XSSYA has a library of encoded payloads To bypass WAF (Web Application Firewall)
- Supports saving the HTML before executing the payload
What’s new in v2.0?
- More payloads; library contains 41 payloads to enhance detection level
- XSS scanner is now removed from XSSYA to reduce false positive
- URLs to be tested used to not allow any character at the end of the URL except (/ – = -?) but now this limitation has been removed
- HTML5 Payloads
- IP Address Conversion (Hex, DWORD, Octal etc)
- XST (Cross Site Tracing) Detection
You can download XSSYA here:
Or read more here.
