XSSYA is a Cross Site Scripting Scanner & Vulnerability Confirmation Tool, it’s written in Python and works by executing an encoded payload to bypass Web Application Firewalls (WAF) which is the first method request and response. If the website/app responds 200 it attempts to use “Method 2” which searches for the payload decoded in the web page HTML code if it confirmed get the last step which is to execute document.cookie to get the cookie.
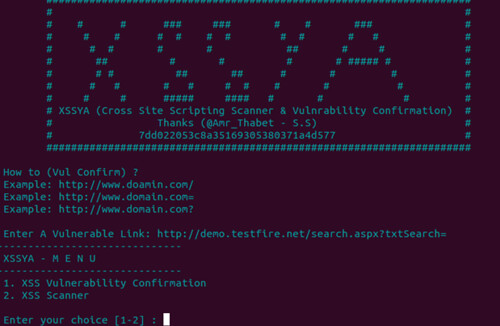
XSSYA Features
- Supports HTTPS
- After Confirmation (execute payload to get cookies)
- Can be run in Windows & Linux
- Identifies 3 types of WAF (mod_security, WebKnight & F5 BIG IP)
- XSSYA Continue Library of Encoded Payloads To Bypass WAF (Web Application Firewall)
- Support Saving The Web HTML Code Before Executing the Payload Viewing the Web HTML Code into the Screen or Terminal
We have written about a couple of XSS related tools before:
– XSS-Proxy – Cross Site Scripting Attack Tool
– XSS Shell v0.3.9 – Cross Site Scripting Backdoor Tool
You can download XSSYA here:
Or read more here.
