This is a pretty interesting use of the Windows Registry and reminds me a little of the transient drive-by malware used last year against Internet Explorer that left no files either – Another IE 0-Day Hole Found & Used By In-Memory Drive By Attacks.
The main difference being, that wasn’t persistent and as it lived in RAM, it wouldn’t survive a reboot. This time, it’s based in the Registry (which technically is stored on the file system) – so it does survive a reboot and is pretty well hidden.
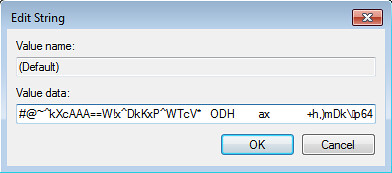
The malware itself is stored in the registry in a non-ASCII key (to hide it from autostart) and an encoded entry that can’t be properly read by Regedit.
Researchers have detailed a rare form of malware that maintains infection on machines and steals data without installing files.
The malware resides in the computer registry only and is therefore not easy to detect.
It code reaches machines through a malicious Microsoft Word document before creating a hidden encoded autostart registry key, malware researcher and black hat exterminator Paul Rascagneres (@r00tbsd) says. It then creates and executes shellcode and a payload Windows binary.
“All activities are stored in the registry. No file is ever created,” Rascagneres said in a post. “So, attackers are able to circumvent classic anti-malware file scan techniques with such an approach and are able to carry out any desired action when they reach the innermost layer of [a machine] even after a system re-boot.
“To prevent attacks like this, anti-virus solutions have to either catch the initial Word document before it is executed (if there is one), preferably before it reached the customer’s email inbox.”
Windows Regedit cannot read or open the non-ASCII key entry. Rascagneres said the feature set was akin to a Matryoshka Doll due to its subsequent and continual ‘stacked’ execution of code.
The researcher doing this work is pretty well known for tearing down blackhat/malware networks, you can follow him (Paul Rascagneres) on Twitter here, and should (he’s interesting): @r00tbsd.
It’ll be interesting to see if any even smarter variations are spawned from this, or if Microsoft does anything to stop it from working (although they rarely do anything related to malware unless it’s using an actual exploited vulnerability).
The non-ASCII trick is a tool Microsoft uses to hide its source code from being copied, but the feature was later cracked.
Security kit can alternatively detect the software exploit, or as a final step monitor the registry for unusual behaviour, he said.
Malware geeks on the KernelMode.info forum last month analysed one sample which exploited the flaws explained in CVE-2012-0158 that affected Microsoft products including Office.
Deviants distributed the malware under the guise of Canada Post and UPS emails purportedly carrying tracking information.
“This trick prevents a lot of tools from processing this malicious entry at all and it could generate a lot of trouble for incident response teams during the analysis. The mechanism can be used to start any program on the infected system and this makes it very powerful,” Rascagneres said.
Rascagneres has made a name ripping malware and bots to uncover and undermine black hat operations. He won last years’ Pwnie Award at Black Hat Las Vegas for tearing through the infrastructure of Chinese hacker group APT1.
The malware is technically pretty smart (And well obfuscated) as it has layers of execution, the initial code executed is JScript code and then it runs a PowerShell script which finally executes shellcode.
You can read the original post here: Poweliks: the persistent malware without a file
The Irony? This encoding technique was originally made by Microsoft themselves..to protect source code from being changed/tampered with.
Source: The Register

Fábio Pinto Coelho says
The article of the The Register is somewhat flawed. It mentions that “The non-ASCII trick is a tool Microsoft uses to hide its source code from being copied, but the feature was later cracked.”, but what MS uses to hide source code is not the non-ASCII trick, but the script encoding scheme (see JScript.Encode on Wikipedia) for protecting JScript, VBScript etc.
The trick used by the malware, although ingenious, is not exploiting any flaw in Windows for running, but only for hiding itself from the end-user. If it can be programmatically inserted into the registry, it can also be programmatically detected by AV tools which are not limited to ASCII characters.
Darknet says
Yah, I tried to clarify a little in what I wrote, the non-ASCII trick just hides that character (which looks like a Chinese word) from Autostart. The encoding itself the JScript as you say.
I’m sure it’ll be detected before too long.