Yes finally, like 6 years later than everyone else we have a Facebook page – it has a huge 3 likes.. I’ll share the posts there (if you don’t use RSS any more since Google Reader closed down – it might be a decent way to keep up) plus some other funny/interesting stuff of relevance […]
Archives for February 2014
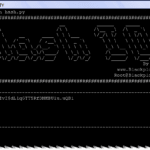
Hash Identifier – Identify Types Of Hashes Used To Encrypt Passwords
Hash Identifier or HashID is a Python-based tool that allows you to quickly identify types of hashes used to encrypt passwords. It supports over 220 unique hash types using regular expressions. Somewhat similar to HashTag – Password Hash Type Identification (Identify Hashes) – which we posted about a while back. It is able to identify […]
A Story Of Social Engineering – How @N Lost His $50,000 Twitter Handle
So last week I read an interesting tale about social engineering on Medium, a story by a chap named Naoki Hiroshima and his Twitter handle, which was @N. Yes just one letter, a pretty rare and it seems valuable handle as he had offers of up to $50,000 for it. In the end though, someone […]