The Refog Free Keylogger, KGB Keylogger is a decent light weight Key Logger for Windows which has a stealth mode, logs the clipboard and much more.
What is The Best Free Keylogger – KGB
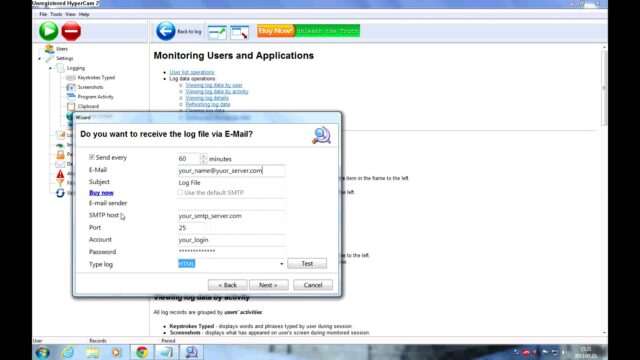
The Refog Free KGB Key logger is a multi-functional keyboard tracking software that is widely used by both regular users and IT security specialists for tracking the key strokes typed on a given machine.
Refog Free Keylogger KGB Key logger Features
- Stealth mode and visible mode of work;
- Logs keyboard input, including language-specific characters;
- Logs Clipboard entries;
- Monitors and logs network activities;
- Custom list of monitored applications;
- Detailed information for each log entry, including the time stamp, application name and window caption;
- Screenshots at custom frequency (regular intervals or on mouse clicks);
- Export of logs into HTML;
The software works as described and is pretty fully featured for a Keylogger including a screen capture feature, not just the normal text/keyboard capturing facility.
The interface is nice and it’s fairly easy to use.
There are also much more advanced RAT type tools which include Keylogging capabilites such as Stitch – Python Remote Administration Tool AKA RAT.
Download Refog Free Keylogger KGB
You can download the trial version here (Valid for 7 days):
KGB Keylogger is priced reasonably at the current discount rate of $42USD, you can read more here or buy it now here.
You can purchase it securely online with a PayPal, Credit Card, Bank/Wire Transfer, Phone, Fax, Mail/Check and Corporate Purchase orders.

CK76 says
We use Sophos antivirus where I work, and this is picked up by it. I don’t know about other antivirus products, but I’m sure they do to.
Daniel says
anything can be made undetected CK76
TheRealDonQuixote says
@ Daniel
Most keyloggers are easily found by anti-vir soft, cause they are very small, not much code, and thusly very very easy to identify. Any anti-vir using heristics will find pretty much any keylogger file that is an executable. Now as far as rootkits… That’s a different story.
Sandeep Nain says
Other than that (detectable by anti virus), very nice piece of software with extremely cool GUI. very very easy to use…
Navin says
@ Sandeep, the fact that it is detected by antiviruses (in my case both AVG and PC-Cilin) detected it, makes it totally useless……its sorta like a ninja who moves about in the open (and wearing a transparent mask)
@ TheRealDonQuixote, is it possible to pair up a keylogger and a rootkit, to somehow disable the antivirus, perhaps prevent the antivirus engines from loading into system memory(or prevent realtime scanning) maybe , and then running the keylogger to execute upon the next system restart (as at present, the antivirus engine will be already running and will probably detect it when it executes……atleast tht’s wht happens on the PC I work on….the executable is detected in few cases unless it is executed!!)
What say??