Wfuzz is a Python-based flexible web application password cracker or brute forcer which supports various methods and techniques to expose web application vulnerabilities. This allows you to audit parameters, authentication, forms with brute-forcing GET and POST parameters, discover unlinked resources such as directories/files, headers and so on.
A brute force attack is a method to determine an unknown value by using an automated process to try a large number of possible values.
What is Wfuzz Bruteforcer?
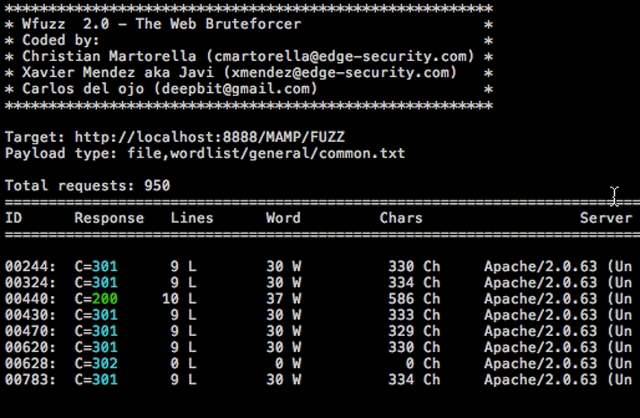
Wfuzz was created to facilitate the task in web applications assessments and it is based on a simple concept: it replaces any reference to the keyword FUZZ by the value of a given payload. A payload in Wfuzz is a source of input data.
This simple concept allows any input to be injected in any field of an HTTP request, allowing to perform complex brute force attacks in different web application components such as: parameters, authentication, forms, directories/files, headers, etc.
You can use it to find several type of vulnerabilities:
- Predictable credentials
- Predictable sessions identifier (session idʼs)
- Predictable resource location (directories and files)
- Injections
- Path traversals
- Overflows
- Cross site scripting
- Authentication flaws
- Insecure direct object references
Wfuzz Password Cracker Features
Wfuzz was created to facilitate the task in web applications assessments, a tool by pen-testers for pen-testers.
- Recursion (when doing directory discovery)
- Post data brute-forcing
- Header brute-forcing
- Output to HTML (easy for just clicking the links and checking the page, even with postdata!)
- Colored output
- Hide results by return code, word numbers, line numbers, etc.
- Url encoding
- Cookies
- Multithreading
- Proxy support
- All parameter fuzzing
How to use Wfuzz Password Cracker
Example:
|
1 |
wfuzz.py -c -z file -f commons.txt --hc 404 --html http://www.mysite.com/FUZZ |
You can also check out:
– Patator – Multi Purpose Brute Forcing Tool
– Medusa v1.5 Released – Parallel, Modular Login Brute Forcing Tool
– THC Hydra Download – Fast & Flexible Network Login Hacking Tool
You can download Wfuzz here:
Or read more here.
