[ad]
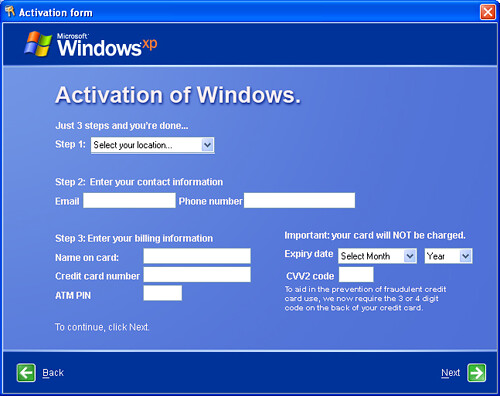
Recently a new Trojan popped up that mimics the Windows activation interface, phishing for credit card details and even the PIN number.
The Trojan itself isn’t particularly advanced technically, it’s mostly just a social engineering attack.
Symantec is reporting on a Trojan horse that mimics the Windows activation interface.
What they are calling Trojan.Kardphisher doesn’t do most of the technical things that Trojan horses usually do; it’s a pure social engineering attack, aimed at stealing credit card information. In a sense, it’s a standalone phishing program.
Once you reboot your PC after running the program, the program asks you to activate your copy of Windows and, while it assures you that you will not be charged, it asks for credit card information. If you don’t enter the credit card information it shuts down the PC. The Trojan also disables Task Manager, making it more difficult to shut down..
It’s a pretty interesting attack and it shows malware creators are getting more innovative, rather than looking for technical solutions and how to hide their key-loggers etc. they are just looking at ways to make the interface look more legitimate so unwary users give their information away themselves.
Running on the first reboot is clever. It inherently makes the process look more like it’s coming from Windows itself, and it removes the temporal connection to running the Trojan horse. The program even runs on versions of Windows prior to XP, which did not require activation.
This is not an attack that will sneak by you. The executable is nearly 1MB large. But if you find yourself in this situation you should be able to disable it in Windows Safe mode by removing the registry keys described in the Symantec writeup and deleting the program it points to. Updated antivirus software should also be able to remove it.
You can also read more about the Trojan on the Symantec page:
Source: PCMag

Bogwitch says
Again, some old news – the Symantec report is from April!
However it does raise some interesting possibilities. What’s next? Replacing MS Office components with Trojan startup? Other applications?
Darknet says
Bogwitch: Yeah this was noted a while back, but got passed over. It’s still interesting and relevant in the evolution of Malware though.
Sandeep nain says
Well.. its a shame that people are still unaware and usualy get stung with such malwares….
SN says
This is cool.
-SN