BackTrack is the result of the merging of the two innovative penetration testing live linux distributions Auditor security collection and Whax. By combining the best features from both distributions and putting continous development energy, the most complete and finest security testing live distro was born: BackTrack
BackTrack v.2.0 is finally released, it’s been a long wait that’s for sure, it does look good though so perhaps it was worth waiting.
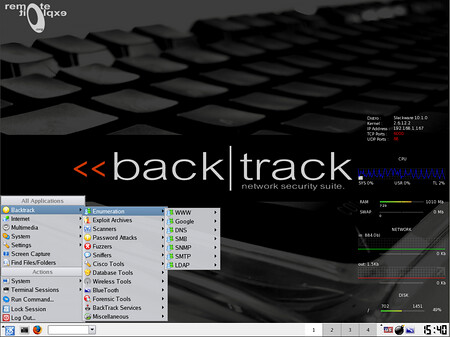
You can find some screenshots here.
BackTrack ranked number one in Darknet’s well regarded list 10 Best Security Live CD Distros (Pen-Test, Forensics & Recovery).
It’s taken BackTrack almost 5 months to pull themselves out of the beta stage. Many features have been added and many of the persistent bugs have been fixed.
New exciting features in BackTrack 2, to mention a few:
- Updated Kernel-Running 2.6.20, with several patches.
- Broadcom based wireless card support
- Most wireless drivers are built to support raw packet injection
- Metasploit2 and Metasploit3 framework integration
- Alignment to open standards and frameworks like ISSAF and OSSTMM
- Redesigned menu structure to assist the novice as well as the pro
- Japanese input support-reading and writing in Hiragana / Katakana / Kanji.
As usual, Nessus is not included into BackTrack as Tenable forbid redistribution.
The public wiki project is available at http://backtrack.offensive-security.com. Please help us by providing entries in HCL (Hardware compatibility list).
Read more about BackTrack here.
You can download BackTrack here:

honest lawyer says
OK this all sounds great, but wont using this unwittingly win me eyes from echelon, the feds, interpol and all the other Bablyonians? Why is there no legality info on their homepage?Will visiting their homepage without proxy also win you a slot in echelon servers? I’m curious, the world is twitchy nervous these days, with all the bad things nice people do to each other ‘n all
TheRealDonQuixote says
@ Honest Lawyer
BackTrack is a security/penetration testing linux distro. Nothing illegal about the actual site or download at all, its how you use it that matters. It is pretty much basic knowledge that one crosses the line into being legally at risk, when one compromises a system that they either do not own or have written permission from the owner. Of course the laws around the hacking issues are pretty hard to enforce, kinda like bittorrent DL’s. In short, you’re totally safe unless you hack into the pentagon’s servers and you’re NOT in china ;)
As for Echelon et al, no worries, I’ve been on their watchlist/scanned by all sorts of “secret” gov’t servers for a couple years now. And I have yet to be incarcerated. Darknet got a takedown notice for posting “Brutus Password Cracker” but that was it, as far as I know.
Basically, all those peeps that you are worried about, are either completely incompetent or they don’t care unless a large business entity gets all pissed and starts suing people like the RIAA/MPAA. Gov’ts know who butters their bread.
So feel free to learn away while hacking.
Sandeep Nain says
honest lawyer: Backtrack should be considered as a set of tools to be used by penetration testers to test the security of the information systems so that any vulnerability found can be fixed before it gets exploited by the attackers
.. and I believe as long as you are using the tools to secure the systems and not doing anything illegal… it doesnt matter if you may get spotted by echeleon servers or FBI…
and as TRDQ said:you
Ami says
Hi,
I have downloaded some stuff for wireless hacking live CD but enable to play it .I am using windows vista machine and it is having an file KNOPIX of 631mb Please assist how to run this.As we think it is a CD from Auditor security collection.
Thanks & regards
Amit
Sleepy says
Amit, at first glance it seems you are writing the file to the disk as data instead of burning it as an image? Or maybe you’re trying to load a bootable OS disk while still an OS? Regardless, I have a hard time believing this OS and its tools will do you much good, forgive me if I’m making a false judgment, but if you cant get the cd to work I don’t think you posses the expertise and understanding to use it. If you have a serious situation concerning network penetration testing or forensics you should contact a professional. If it’s academic, well, have fun. ;) If you still need help, post again with more specific information and I’ll try to help you.
gomika says
Hi guys,. is there any tutorial how to use this live cd?