Stardox is a Python-based GitHub stargazers information gathering tool, it scrapes Github for information and displays them in a list tree view. It can be used for collecting information about your or someone else’s repository stargazers details. GitHub allows visitors to star a repo to bookmark it for later perusal. Stars represent a casual interest […]
information gathering
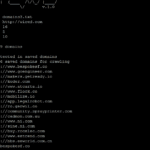
GetAltName – Discover Sub-Domains From SSL Certificates
GetAltName it’s a little script to discover sub-domains that can extract Subject Alt Names for SSL Certificates directly from HTTPS websites which can provide you with DNS names or virtual servers. It’s useful in a discovery phase of a pen-testing assessment, this tool can provide you with more information about your target and scope. Features […]
dcrawl – Web Crawler For Unique Domains
dcrawl is a simple, but smart, multithreaded web crawler for randomly gathering huge lists of unique domain names. How does dcrawl work? dcrawl takes one site URL as input and detects all a href= links in the site’s body. Each found link is put into the queue. Successively, each queued link is crawled in the […]
GitMiner – Advanced Tool For Mining Github
GitMiner is an Advanced search tool for automation in Github, it enables mining Github for useful or potentially dangerous information or for example specific vulnerable or useful WordPress files. This tool aims to facilitate mining the code or snippets on Github through the site’s search page. What is Mining Github? GitHub is a web-based Git […]
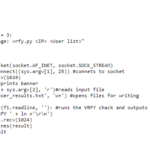
PenTools – Penetration Testing Tools Bundle
PenTools is a bundle of Python and Bash penetration testing tools for the recon and information gathering stage of a PT or VA. They are fairly simple scripts but might be interesting if you are new and want to see how some things are done, or how things can be automated using Python or Bash. […]