The evolution of the internet has been rapid over the years and has impacted the privacy implications of Web 3.0 and Darknets
Privacy
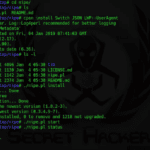
Nipe – Make Tor Default Gateway For Network
Nipe is a Perl script to make Tor default gateway for network, this script enables you to directly route all your traffic from your computer to the Tor network through which you can surf the internet anonymously without having to worry about being tracked or traced back. Tor enables users to surf the internet, chat […]
Eraser – Windows Secure Erase Hard Drive Wiper
Eraser is a hard drive wiper for Windows which allows you to run a secure erase and completely remove sensitive data from your hard drive by overwriting it several times with carefully selected patterns. Eraser is a Windows focused hard drive wiper and is currently supported under Windows XP (with Service Pack 3), Windows Server […]
Instagram Leak From API Spills High Profile User Info
Another high profile Instagram leak, this time no there’s actual tangible repercussions other than it could possibly link to the recent Justin Bieber nudes leaked via a compromise of Selena Gomez’s account. There isn’t a whole lot of details about what actually happened, in terms of what went wrong with the API? A wild guess […]
Should US Border Cops Need a Warrant To Search Devices?
The answer from me is, OF COURSE, f&ck yes. They can’t search your home, car and anywhere else in the country, they would need a warrant to search devices too. A case by the EFF (Electronic Frontier Foundation) is heading to the Fifth Circuit Court of Appeals in the US to find out what should […]