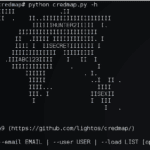
Credmap is an open source credential mapper tool that was created to bring awareness to the dangers of credential reuse. It is capable of testing supplied user credentials on several known websites to test if the password has been reused on any of these. It is not uncommon for people who are not experts in […]
Privacy
OneLogin Hack – Encrypted Data Compromised
The OneLogin hack is blowing up now it seems like whoever got access can also decrypt encrypted customer data which is just about AS BAD as it can get for a password/identity management service. Now I’m a HUGE supporter of password management tools as I’ve mentioned many times here, so anyone who signed up for […]
UK Schedule 7 – Man Charged For Not Sharing Password
Finally UK Schedule 7 of the Terrorism Act 2000 is finally being enacted and is no longer an idle threat, so be aware it’s not only the USA that has these kind of draconian laws. A man who refused to share his phone and laptop passwords has been charged under Schedule 7, which is pretty […]
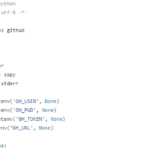
Github Dorks – Github Security Scanning Tool
Github search is quite a powerful and useful feature and can be used to search for sensitive data in repositories, this Github security scanning tool comes with a collection of Github dorks that can reveal sensitive personal and/or other proprietary organisational information such as private keys, credentials, authentication tokens and so on. github-dork.py is a […]
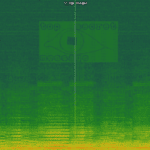
spectrology – Basic Audio Steganography Tool
spectrology is a Python-based audio steganography tool that can convert images to audio files with a corresponding spectrogram encoding, this allows you to hide hidden messages via images inside audio files. Using this tool you can select range of frequencies to be used and all popular image codecs are supported. Usage
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 |
usage: spectrology.py [-h] [-o OUTPUT] [-b BOTTOM] [-t TOP] [-p PIXELS] [-s SAMPLING] INPUT positional arguments: INPUT Name of the image to be converted. optional arguments: -h, --help show this help message and exit -o OUTPUT, --output OUTPUT Name of the output wav file. Default value: out.wav). -b BOTTOM, --bottom BOTTOM Bottom frequency range. Default value: 200. -t TOP, --top TOP Top frequency range. Default value: 20000. -p PIXELS, --pixels PIXELS Pixels per second. Default value: 30. -s SAMPLING, --sampling SAMPLING Sampling rate. Default value: 44100. |
Example
|
1 |
python spectrology.py test.bmp -b 13000 -t 19000 |
You […]