It’s been a while since the last major release of Nmap, the last time we reported on it was when Nmap v5.20 was Released (February 2010). The latest major version has just been released, version 6 – and is now available for download!
For the two people on the planet who don’t know – Nmap (“Network Mapper”) is a free and open source utility for network discovery and security auditing. Many systems and network administrators also find it useful for network inventory, managing service upgrade schedules, monitoring host or service uptime, and many other tasks. Nmap uses raw IP packets in novel ways to determine what hosts are available on the network, what services (application name and version) those hosts are offering, what operating systems (and OS versions) they are running, what type of packet filters/firewalls are in use, and dozens of other characteristics.
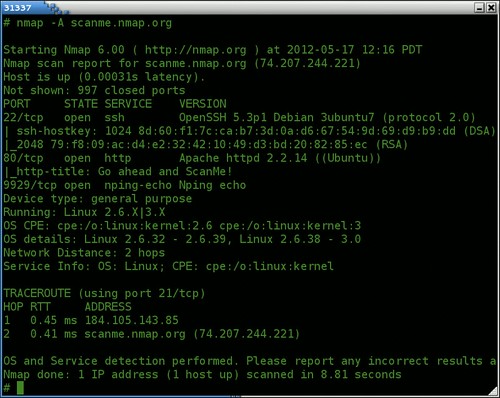
It was designed to rapidly scan large networks, but works fine against single hosts. Nmap runs on all major computer operating systems, and official binary packages are available for Linux, Windows, and Mac OS X. In addition to the classic command-line Nmap executable, the Nmap suite includes an advanced GUI and results viewer (Zenmap), a flexible data transfer, redirection, and debugging tool (Ncat), a utility for comparing scan results (Ndiff), and a packet generation and response analysis tool (Nping).
Major Improvements in v6.00
- NSE Enhanced – The Nmap Scripting Engine (NSE) has exploded in popularity and capabilities. This modular system allows users to automate a wide variety of networking tasks, from querying network applications for configuration information to vulnerability detection and advanced host discovery. The script count has grown from 59 in Nmap 5 to 348 in Nmap 6, and all of them are documented and categorized in our NSE Documentation Portal. The underlying NSE infrastructure has improved dramatically as well.
- Better Web Scanning – As the Internet has grown more web-centric, Nmap has developed web scanning capabilities to keep pace. When Nmap was first released in 1997, most of the network services offered by a server listened on individual TCP or UDP ports and could be found with a simple port scan. Now, applications are just as commonly accessed via URL path instead, all sharing a web server listening on a single port. Nmap now includes many techniques for enumerating those applications, as well as performing a wide variety of other HTTP tasks, from web site spidering to brute force authentication cracking. Technologies such as SSL encryption, HTTP pipelining, and caching mechanisms are well supported.
- Full IPv6 Support – Given the exhaustion of available IPv4 addresses, the Internet community is trying to move to IPv6. Nmap has been a leader in the transition, offering basic IPv6 support since 2002. But basic support isn’t enough, so we spent many months ensuring that Nmap version 6 contains full support for IP version 6. And we released it just in time for the World IPv6 Launch. We’ve created a new IPv6 OS detection system, advanced host discovery, raw-packet IPv6 port scanning, and many NSE scripts for IPv6-related protocols. It’s easy to use too—just specify the -6 argument along with IPv6 target IP addresses or DNS records. In addition, all of our web sites are now accessible via IPv6. For example, Nmap.org can be found at 2600:3c01::f03c:91ff:fe96:967c.
- New Nping Tool – The newest member of the Nmap suite of networking and security tools is Nping, an open source tool for network packet generation, response analysis and response time measurement. Nping can generate network packets for a wide range of protocols, allowing full control over protocol headers. While Nping can be used as a simple ping utility to detect active hosts, it can also be used as a raw packet generator for network stack stress testing, ARP poisoning, Denial of Service attacks, route tracing, etc. Nping’s novel echo mode lets users see how packets change in transit between the source and destination hosts. That’s a great way to understand firewall rules, detect packet corruption, and more.
- Better Zenmap GUI results viewer – While Nmap started out as a command-line tool and many (possibly most) users still use it that way, we’ve also developed an enhanced GUI and results viewer named Zenmap. One addition since Nmap 5 is a “filter hosts” feature which allows you to see only the hosts which match your criteria (e.g. Linux boxes, hosts running Apache, etc.) We’ve also localized the GUI to support five languages besides English. A new script selection interface helps you find and execute Nmap NSE scripts. It even tells you what arguments each script supports.
- Faster scans – In Nmap’s 15-year history, performance has always been a top priority. Whether scanning one target or a million, users want scans to run as fast as possible without sacrificing accuracy. Since Nmap 5 we’ve rewritten the traceroute system for higher performance and increased the allowed parallelism of the Nmap Scripting Engine and version detection subsystems. We also performed an intense memory audit which reduced peak consumption during our benchmark scan by 90%. We made many improvements to Zenmap data structures and algorithms as well so that it can now handle large enterprise scans with ease.
You can download Nmap v6.00 here:
Linux: nmap-6.00.tar.bz2
Windows: nmap-6.00-win32.zip
Or read more here.

Nasruminallah Zeeshan says
Yeah, I have installed Nmap 6 already compiling from Source Code, its awesome, with improved performance and nslibs and scripts. Cool
bonjo says
is this software a hacking tool? if it is, what does it do?…can it hack mobile device?..