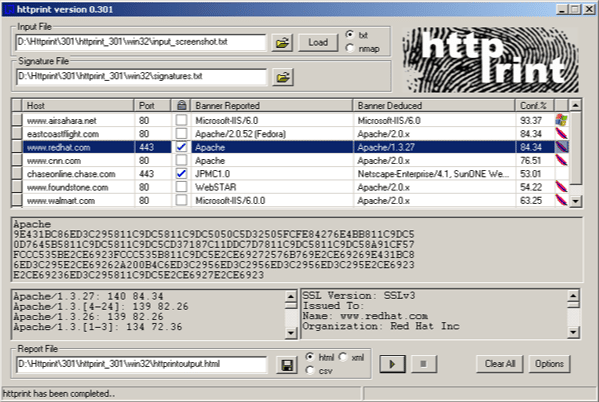
httprint is a web server fingerprinting tool. I was looking through my toolbox to see what else is useful and I came across this one, httprint – the only caveat is that it’s a little out of date. It still does a good job though.
How does httprint work?
It relies on web server characteristics to accurately identify web servers, despite the fact that they may have been obfuscated by changing the server banner strings, or by plug-ins such as mod_security or servermask. httprint can also be used to detect web enabled devices which do not have a server banner string, such as wireless access points, routers, switches, cable modems, etc. httprint uses text signature strings and it is very easy to add signatures to the signature database.
More details on how httprint works can be found in the Introduction to HTTP fingerprinting paper. It is printer-friendly.
Main Features of httprint
- Identification of web servers despite the banner string and any other obfuscation. It can successfully identify the underlying web servers when their headers are mangled by either patching the binary, by modules such as mod_security.c or by commercial products such as ServerMask.
- Inventorying of web enabled devices such as printers, routers, switches, wireless access points, etc. Click on the sample HTML report.
- Customisable web server signature database. To add new signatures, simply cut and paste the output against unknown servers into the signatures text file.
- Confidence Ratings. It now picks the best matches based on confidence ratings, derived using a fuzzy logic technique, instead of going by the highest weight. More details on the significance of confidence ratings can be found in section 8.4 of the Introduction to HTTP fingerprinting paper.
- Multi-threaded engine. Version 301 is a complete rewrite, featuring a multi-threaded scanner, to process multiple hosts in parallel. This greatly saves scanning time.
- SSL information gathering. It now gathers SSL certificate information, which helps you identify expired SSL certificates, cyphers used, certificate issuer, and other such SSL related details.
- Automatic SSL detection. It can detect if a port is SSL enabled or not, and can automatically switch to SSL connections when needed.
- Automatic traversal of HTTP 301 and 302 redirects. Many servers who have transferred their content to other servers send a default redirect response towards all HTTP requests. httprint now follows the redirection and fingerprints the new server pointed to. This feature is enabled by default and can be turned off, if needed.
You can download httprint here:
Win32 – httprint_win32_301.zip
Linux – httprint_linux_301.zip
Or you can read more here.
