So what is wild on the web this year? Need to know about the most critical web vulnerabilities in 2019 to protect your organization?
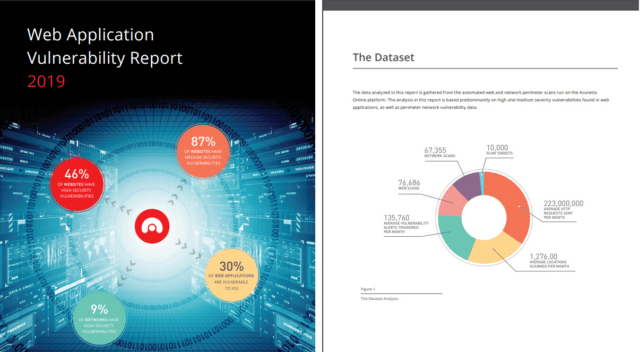
Well luckily for you Acunetix compiles an annual web application vulnerability report which is a fairly hefty piece of analysis on data gathered from the previous year. This is compiled from the automated web and network perimeter scans run on the Acunetix Online platform, over a 12 month period, across more than 10,000 scan targets.
To be more specific:
- 67,355 Network scans
- 10,000 Scan targets
- 76,686 Web scans
It was found that as many that almost half of the scanned websites contain high severity vulnerabilities with almost all containing medium severity vulnerabilities.
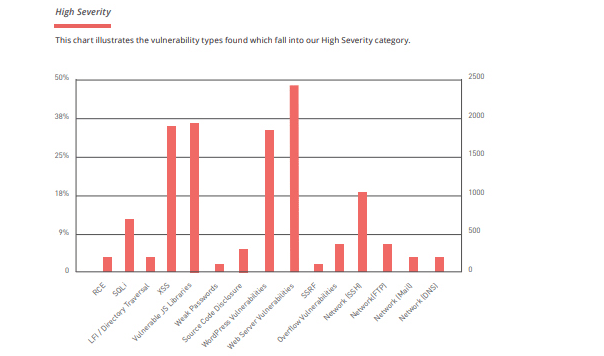
Although SQL Injection vulnerabilities are on the slight decline, XSS vulnerabilities, vulnerable JavaScript libraries, and WordPress related issues were found to each claim a significant 30% of the sampled targets.
What are the most critical web vulnerabilities in 2019?
The report gives you the low down on:
- Which vulnerabilities are rising and falling in frequency
- Current security concerns, such as the increasing complexity of new apps, the accelerating rate of new versions, and the problem of scale
- Changes in threat landscape from both the client and server sides
- The four major stages of vulnerability analysis
- Vulnerability findings by type and severity
- An analysis of each discovered vulnerability in terms of how it works, its statistical status and pointers for remediation.
So, top line message – keep yourself safe!
You can download the full report here:
