Netsparker just published some anonymized Web Security Stats about the security vulnerabilities their online solution identified on their users’ web applications and web services during the last 3 years.
Data-based stats like these, which are not based on surveys, can be pretty useful – at least to get a broad overview of what is going on. These statistics also serve a solid purpose – they help all developers, security professionals and anyone who works with web applications better understand what might be going wrong.
XSS is way more common than SQL Injection
SQL Injection has been the most critical web application vulnerability in the last decade according to the OWASP Top 10 list of most critical web application security flaws (yeah come-on guys, we are still waiting for the new version!). Though the Netsparker statistics show us that it is the other way round, at least in terms of volume.
26% of the identified vulnerabilities, 40,908 to be exact, were a mix of reflected and DOM Cross-site scripting (XSS) vulnerabilities. Only 2% of the identified vulnerabilities were SQL Injections.
That is a big discrepancy, though this is not a surprise according to the authors. They said:
Developers have a lot of resources to write code that is not vulnerable to SQL Injections, such as prepared statements. New frameworks by default protects against SQL Injection and makes it quite hard to write insecure SQL code. On the other hand XSS vulnerabilities are much more complex to address and even when the framework has built-in protection, it’s very easy to make mistakes
Outdated & vulnerable software is still a major web application security risk
Update your apps, your server, your software – Apple, Google, Microsoft are constantly harping on this topic but it doesn’t seem to help that much.
It’s one of the easiest best practices to follow, especially in modern times with automated updates and patch management software easily available.
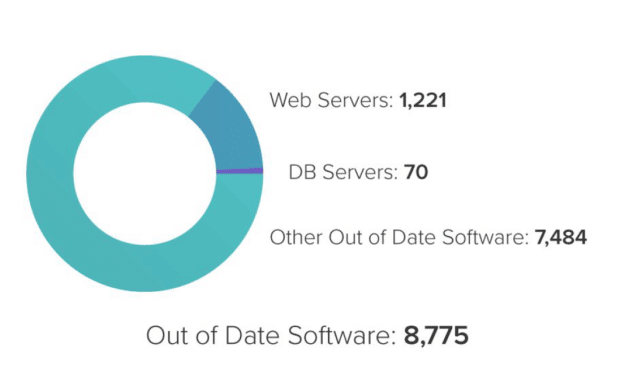
It seems not to be the case that people are following it with 5% of the identified issues related to outdated software.
If Equifax and Mossack Fonseca had their software up to date, last year we wouldn’t have had two of the biggest data breaches on the internet.
Accuracy is key to more secure web applications
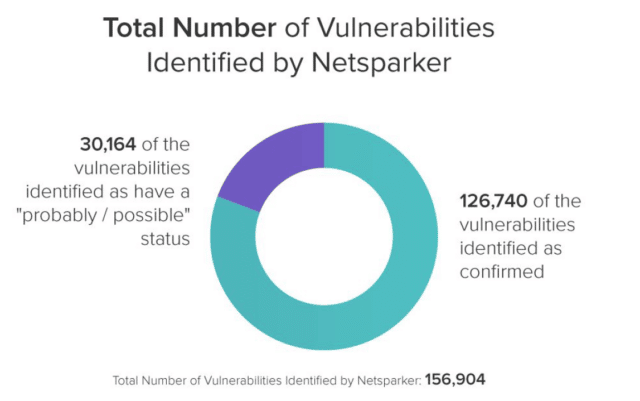
There are several other statistics from which we can learn something from, an interesting one for me was the fact that Netsparker automatically verified around 80% of the identified vulnerabilities.
False positives are a big problem in automated vulnerability and security scanning as someone has to manually spend hours verifying the results and weeding out the false positives. With Netsparker automatically doing this, a smaller team can do more effective work and a larger team can be more productive doing less manual verification.
Read The Netsparker Scan Web Security Stats Report
The report is much more detailed and has much more statistics, so please read the Netsparker scan statistics report for all the numbers and common security issues that make web applications vulnerable to malicious hacker attacks and can save you from some embarrassment.
