CHIPSEC is a platform security assessment framework for PCs including hardware, system firmware (BIOS/UEFI), and platform components for firmware hacking.
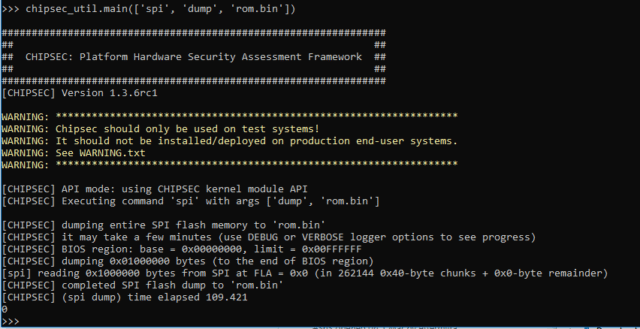
It includes a security test suite, tools for accessing various low-level interfaces, and forensic capabilities. It can be run on Windows, Linux, Mac OS X and UEFI shell.
You can use CHIPSEC to find vulnerabilities in firmware, hypervisors and hardware configuration, explore low-level system assets and even detect firmware implants.
What does CHIPSEC Platform Security Assessment Framework Do?
CHIPSEC has a bunch of modules focusing on areas such as Secure Boot, System Management Mode (SMM/SMRAM), BIOS and Firmware security, BIOS write protection etc.
Modules such as:
– SMRAM Locking
– BIOS Keyboard Buffer Sanitization
– SMRR Configuration
– BIOS Protection
– SPI Controller Locking
– BIOS Interface Locking
– Access Control for Secure Boot Keys
– Access Control for Secure Boot Variables
CHIPSEC Firmware Hacking Warnings
1. CHIPSEC kernel drivers provide direct access to hardware resources to user-mode applications (for example, access to physical memory). When installed on production systems this could allow malware to access privileged hardware resources.
2. The driver is distributed as source code. In order to load it on Operating System which requires kernel drivers to be signed (for example, 64-bit versions of Microsoft Windows 7 and higher), it is necessary to enable TestSigning (or equivalent) mode and sign the driver executable with test signature. Enabling TestSigning (or equivalent) mode turns off an important OS kernel protection and should not be done on production systems.
3. Due to the nature of access to hardware, if any CHIPSEC module issues incorrect access to hardware resources, Operating System can hang or panic.
You can download CHIPSEC here:
Or read more here.
