HTTP is ubiquitous now with pretty much everything being powered by an API, a web application or some kind of cloud-based HTTP driven infrastructure. With that HTTP Security becomes paramount and to secure HTTP you have to understand it.
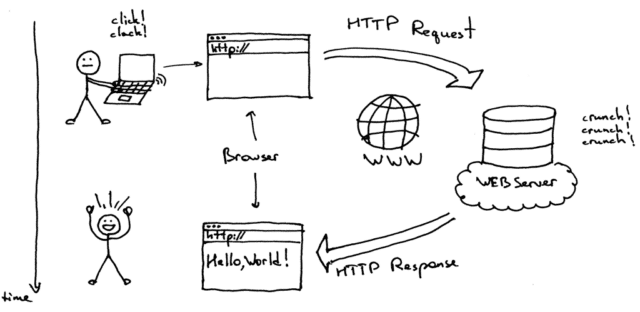
HTTP is the protocol that powers the web and to penetrate via a web service it pays to have a good solid foundational understanding of HTTP, how it works and the common response codes – many of which can lead to some kind of vulnerability which is exploitable.
The Hypertext Transfer Protocol (HTTP) is an application protocol for distributed, collaborative, and hypermedia information systems.[1] HTTP is the foundation of data communication for the World Wide Web.
Hypertext is structured text that uses logical links (hyperlinks) between nodes containing text. HTTP is the protocol to exchange or transfer hypertext.
Development of HTTP was initiated by Tim Berners-Lee at CERN in 1989. Standards development of HTTP was coordinated by the Internet Engineering Task Force (IETF) and the World Wide Web Consortium (W3C), culminating in the publication of a series of Requests for Comments (RFCs). The first definition of HTTP/1.1, the version of HTTP in common use, occurred in RFC 2068 in 1997, although this was made obsolete by RFC 2616 in 1999 and then again by the RFC 7230 family of RFCs in 2014.
Source: Wikipedia
From a security perspective it’s important to understand:
– Requests
– Request methods
– Responses
– Response status codes
All of which are covered in the Security-focused HTTP article by Acunetix.
You can find the article with the full details here:
HTTP Security: A Security-focused Introduction to HTTP, Part 1
