RidRelay is a Python-based tool to enumerate usernames on a domain where you have no credentials by using a SMB Relay Attack with low privileges.
How RidRelay SMB Relay Attack Works
RidRelay combines the SMB Relay attack, common lsarpc based queries and RID cycling to get a list of domain usernames. It takes these steps:
- Spins up an SMB server and waits for an incoming SMB connection
- The incoming credentials are relayed to a specified target, creating a connection with the context of the relayed user
- Queries are made down the SMB connection to the lsarpc pipe to get the list of domain usernames. This is done by cycling up to 50000 RIDs
For best results, use with Responder.
Using RidRelay to Enumerate Usernames
First, find a target host to relay to. The target must be a member of the domain and MUST have SMB Signin off. CrackMapExec can get this info for you very quick!
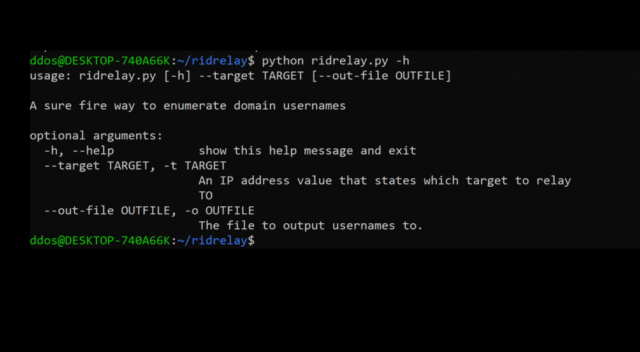
Start RidRelay pointing to the target:
|
1 |
python ridrelay.py -t 10.0.0.50 |
OR
Also output usernames to file
|
1 |
python ridrelay.py -t 10.0.0.50 -o path_to_output.txt |
You can download RidRelay here:
Or read more here.
