Airbash is a POSIX-compliant, fully automated WPA PSK handshake capture script aimed at penetration testing. It is compatible with Bash and Android Shell (tested on Kali Linux and Cyanogenmod 10.2) and uses aircrack-ng to scan for clients that are currently connected to access points (AP).
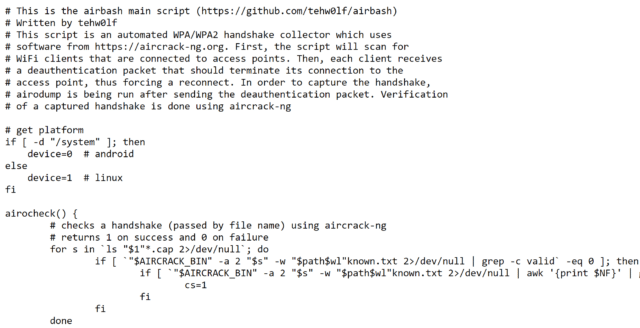
Those clients are then deauthenticated in order to capture the handshake when attempting to reconnect to the AP. Verification of a captured handshake is done using aircrack-ng. If one or more handshakes are captured, they are entered into an SQLite3 database, along with the time of capture and current GPS data (if properly configured).
After capture, the database can be tested for vulnerable router models using crackdefault.sh. It will search for entries that match the implemented modules, which currently include algorithms to compute default keys for Speedport 500-700 series, Thomson/SpeedTouch and UPC 7 digits (UPC1234567) routers.
Calculating Default WPA PSK Keys
After capturing a new handshake, the database can be queried for vulnerable router models. If a module applies, the default keys for this router series are calculated and used as input for aircrack-ng to try and recover the passphrase.
Airbash WPA PSK Handshake Capture Tool Usage
Running install.sh will create the database, prepare the folder structure and create shortlinks to both scripts which can be moved to a directory that is on $PATH to allow execution from any location.
After installation, you may need to manually adjust INTERFACE on line 46 in airba.sh. This will later be determined automatically, but for now the default is set to wlan0, to allow out of the box compatibility with bcmon on Android.
– ./airba.sh starts the script, automatically scanning and attacking targets that are not found in the database.
– ./crackdefault.sh attempts to break known default key algorithms.
To view the database contents, run sqlite3 .db.sqlite3 "SELECT * FROM hs" in the main directory.
You can download Airbash here:
Or read more here.
