Acunetix, the pioneer in automated web application security software, has announced the release of Acunetix v12. This new version provides support for JavaScript ES7 to better analyse sites which rely heavily on JavaScript such as SPAs. This coupled with a new AcuSensor for Java web applications, sets Acunetix ahead of the curve in its ability to comprehensively and accurately scan all types of websites.
With v12 also comes a brand new scanning engine, re-engineered and re-written from the ground up, making Acunetix the fastest scanning engine in the industry.
Acunetix was always in the forefront when it came to accuracy and speed, however now with the re-engineered scanning engine and sensors that support the latest JavaScript and Java technologies, we are seeing websites scanned up to 2x faster without any compromise on accuracy.
– Announced Nicholas Sciberras, CTO.
Acunetix v12 Support for latest JavaScript
Acunetix DeepScan and the Acunetix Login Sequence Recorder have been updated to support ECMAScript version 6 (ES6) and ECMAScript version 7 (ES7). This allows Acunetix to better analyse JavaScript-rich sites which make use of the latest JavaScript features. The modularity of the new Acunetix architecture also makes it much easier now for the technology to stay ahead of the industry curve.
AcuSensor for Java
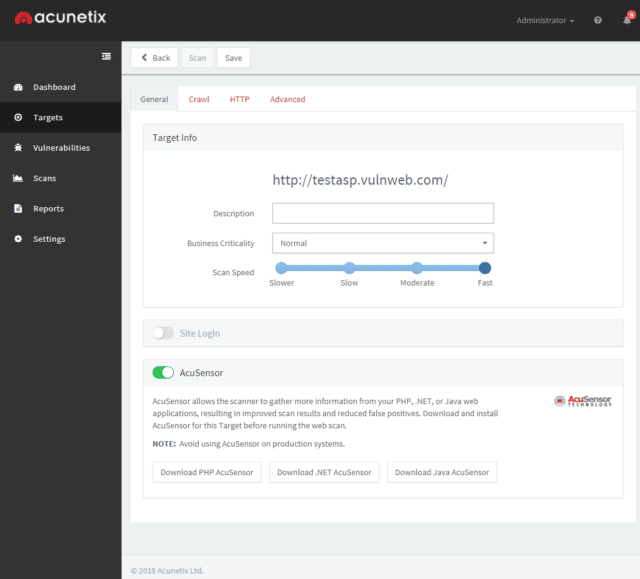
Acunetix version 12 includes a new AcuSensor for Java web applications. This improves the coverage of the web site and the detection of web vulnerabilities, decreases false positives and provides more information on the vulnerabilities identified. While already supporting PHP and ASP .NET, the introduction of Java support in AcuSensor means that Acunetix coverage for interactive gray box scanning of web applications is now possibly the widest in the industry.
Speed and efficiency with Multi-Engine
Combining the fastest scanning engine with the ability to scan multiple sites at a time, in a multi-engine environment, allows users to scan thousands of sites in the least time possible. The Acunetix Multi-engine setup is suitable for Enterprise customers who need to scan more than 10 websites or web applications at the same time. This can be achieved by installing one Main Installation and multiple Scanning Engines, all managed from a central console.
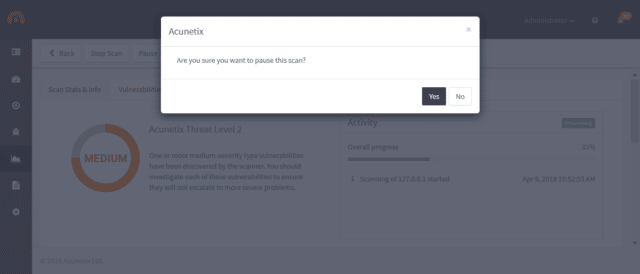
Pause / Resume Feature
Acunetix Version 12 allows the user to pause a Scan and Resume the scan at a later stage. Acunetix will proceed with the scan from where it had left off. There is no need to save any scan state files or similiar – the information about the paused scan is automatically retained in Acunetix.
A trial version can be downloaded from:
