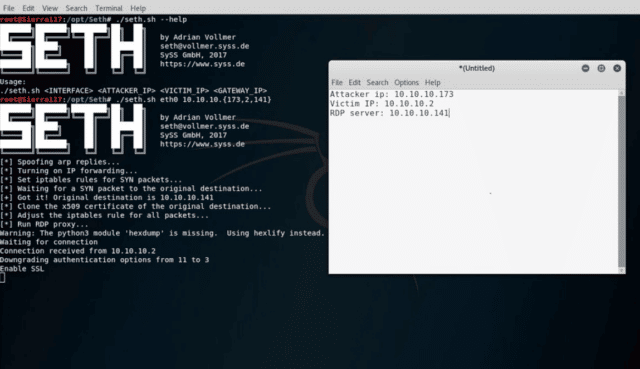
Seth is an RDP Man In The Middle attack tool written in Python to MiTM RDP connections by attempting to downgrade the connection in order to extract clear text credentials.
It was developed to raise awareness and educate about the importance of properly configured RDP connections in the context of pentests, workshops or talks.
Usage of Seth RDP Man In The Middle Attack Tool
Run it like this:
|
1 |
$ ./seth.sh <INTERFACE> <ATTACKER IP> <VICTIM IP> <GATEWAY IP|HOST IP> |
Unless the RDP host is on the same subnet as the victim machine, the last IP address must be that of the gateway.
The script performs ARP spoofing to gain a Man-in-the-Middle position and redirects the traffic such that it runs through an RDP proxy. The proxy can be called separately:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 |
$ ./rdp-cred-sniffer.py -h usage: rdp-cred-sniffer.py [-h] [-d] [-p LISTEN_PORT] [-b BIND_IP] [-g {0,1,3,11}] -c CERTFILE -k KEYFILE target_host [target_port] RDP credential sniffer -- Adrian Vollmer, SySS GmbH 2017 positional arguments: target_host target host of the RDP service target_port TCP port of the target RDP service (default 3389) optional arguments: -h, --help show this help message and exit -d, --debug show debug information -p LISTEN_PORT, --listen-port LISTEN_PORT TCP port to listen on (default 3389) -b BIND_IP, --bind-ip BIND_IP IP address to bind the fake service to (default all) -g {0,1,3,11}, --downgrade {0,1,3,11} downgrade the authentication protocol to this (default 3) -c CERTFILE, --certfile CERTFILE path to the certificate file -k KEYFILE, --keyfile KEYFILE path to the key file |
Requirements for Seth RDP MiTM Attack Tool
- python3
- tcpdump
- arpspoof (arpspoof is part of dsniff)
- openssl < 1.1.0f
OpenSSL should not be too recent, as it does not support older versions of the SSL protocol and thus may be incompatible with older version of the Windows RDP client.
You can check out the full paper here:
– Attacking RDP How to Eavesdrop on Poorly Secured RDP Connections
There’s also another related tool which can extract RDP sessions:
– SessionGopher – Session Extraction Tool
You can download Seth for RDP MiTM here:
Or read more here.
