Cryptocurrency is getting a lot of press lately and some researchers dug a little bit deeper in Bitcoin anonymity as it’s a touted selling point for most cryptocurrencies.
It’s not a problem with Bitcoin itself, or any other coin, more the fact that shopping cart implementations and analytics systems aren’t built with the anonymity of cryptocurrency users in mind.
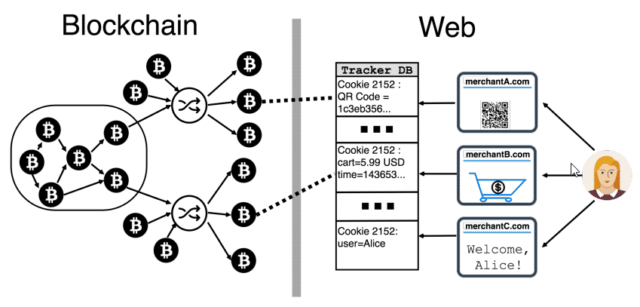
Bitcoin transactions might be anonymous, but on the Internet, its users aren’t – and according to research out of Princeton University, linking the two together is trivial on the modern, much-tracked Internet.
In fact, linking a user’s cookies to their Bitcoin transactions is so straightforward, it’s almost surprising it took this long for a paper like this to be published.
The paper sees privacy researcher Dillon Reisman and Princeton’s Steven Goldfeder, Harry Kalodner and Arvind Narayanan demonstrate just how straightforward it can be to link cookies to cryptocurrency transactions.
Only small amounts of transaction information need to leak, they write, in order for “Alice” to be associated with her Bitcoin transactions. It’s possible to infer the identity of users if they use privacy-protecting services like CoinJoin, a protocol designed to make Bitcoin transactions more anonymous. The protocol aims is to make it impossible to infer which inputs and outputs belong to each other.
So yah I guess if you care about not having your transactions (and/or your wallet) linked to you, be careful what sites you use to transact. Although honestly, I don’t think it’s a huge deal as the way everything works now, it’s very hard to be involved in cryptocurrencies and not be traceable.
All exchanges require identity documents before you can deposit/withdraw, you need an e-mail address to sign in and if you’re buying something online you need some way to receive it either digitally or via a physical address.
Of 130 online merchants that accept Bitcoin, the researchers say, 53 leak payment information to 40 third parties, “most frequently from shopping cart pages,” and most of these on purpose (for advertising, analytics and the like).
Worse, “many merchant websites have far more serious (and likely unintentional) information leaks that directly reveal the exact transaction on the blockchain to dozens of trackers”.
Of the 130 sites the researchers checked:
- In total, 107 sites leaked some kind of transaction information;
- 31 allowed third-party scripts to access users’ Bitcoin addresses;
- 104 shared the non-BTC denominated price of a transaction; and
- 30 shared the transaction price in Bitcoin.
It doesn’t help that even for someone running tracking protection, a substantial amount of personal information was passed around by the sites examined in the study.
If you use the web now, you’re getting tracked, it’s just the way it is. You can block a fair amount of it – but this is just another vector to consider for those who haven’t yet embraced the post-privacy era we live in.
It’s good to see research being done in this area as I think these are things many people might not have thought about.
Source: The Register
