T50 (f.k.a. F22 Raptor) is a high performance mixed packet injector tool designed to perform Stress Testing.
The concept started on 2001, right after release ‘nb-isakmp.c‘, and the main goal was to have a tool to perform TCP/IP protocol fuzzing, covering common regular protocols, such as: ICMP, TCP and UDP.
Why Stress Testing?
Why Stress Testing? Well, because when people are designing a new network infra-structure (e.g. Data center serving to Cloud Computing) they think about:
- High-Availability
- Load Balancing
- Backup Sites (Cold Sites, Hot Sites, and Warm Sites)
- Disaster Recovery
- Data Redundancy
- Service Level Agreements
But almost nobody thinks about Stress Testing, or even performs any test to check how the networks infra-structure behaves under stress, under overload, and under attack. Even during a Penetration Test, people prefer not running any kind of Denial-of-Service testing. Even worse, those people are missing one of the three key concepts of security that are common to risk management:
- Confidentiality
- Integrity
- AVAILABILITY
T50 was designed to perform Stress Testing on a variety of infra-structure network devices (Version 2.45), using widely implemented protocols, and after some requests it was was re-designed to extend the tests (as of Version 5.3), covering some regular protocols (ICMP, TCP and UDP), some infra-structure specific protocols (GRE, IPSec and RSVP), and some routing protocols (RIP, EIGRP and OSPF).
Features
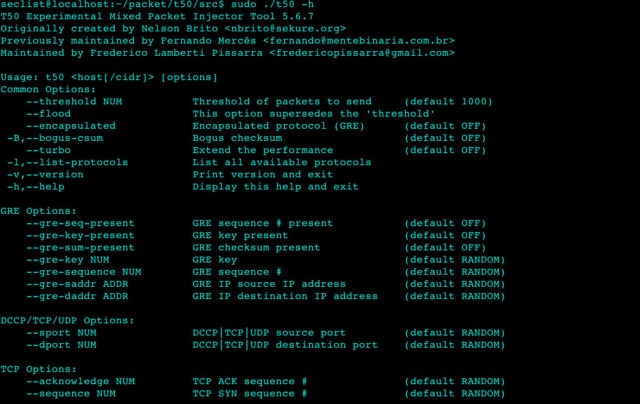
T50 is a powerful and unique packet injector tool, which is capable of sending sequentially the following fourteen protocols:
- ICMP – Internet Control Message Protocol
- IGMPv1 – Internet Group Management Protocol v1
- IGMPv3 – Internet Group Management Protocol v3
- TCP – Transmission Control Protocol
- EGP – Exterior Gateway Protocol
- UDP – User Datagram Protocol
- RIPv1 – Routing Information Protocol v1
- RIPv2 – Routing Information Protocol v2
- DCCP – Datagram Congestion Control Protocol
- RSVP – Resource ReSerVation Protocol
- GRE – Generic Routing Encapsulation
- IPSec – Internet Protocol Security (AH/ESP)
- EIGRP – Enhanced Interior Gateway Routing Protocol
- OSPF – Open Shortest Path First
It is the only tool capable to encapsulate the protocols (listed above) within Generic Routing Encapsulation (GRE).
It can also send an (quite) incredible amount of packets per second, making it a second to none tool:
- More than 1,000,000 pps of SYN Flood (+50% of the network uplink) in a 1000BASE-T Network (Gigabit Ethernet).
- More than 120,000 pps of SYN Flood (+60% of the network uplink) in a 100BASE-TX Network (Fast Ethernet).
Perform Stress Testing on a variety of network infrastructure, network devices and security solutions in place.
And also Simulate “Distributed Denial-of-Service” & “Denial-of-Service” attacks, validating Firewall rules, Router ACLs, Intrusion Detection System and Intrusion Prevention System policies.
The main differentiation of the T50 is that it is able to send all protocols, sequentially, using one single SOCKET, besides it is capable to be used to modify network routes, letting IT Security Professionals perform advanced Penetration Tests.
You can download T50 here:
Or read more here.
