Ghost Phisher is a Wireless and Ethernet security auditing and phishing attack tool written using the Python Programming Language and the Python Qt GUI library, the program is able to emulate access points and deploy.
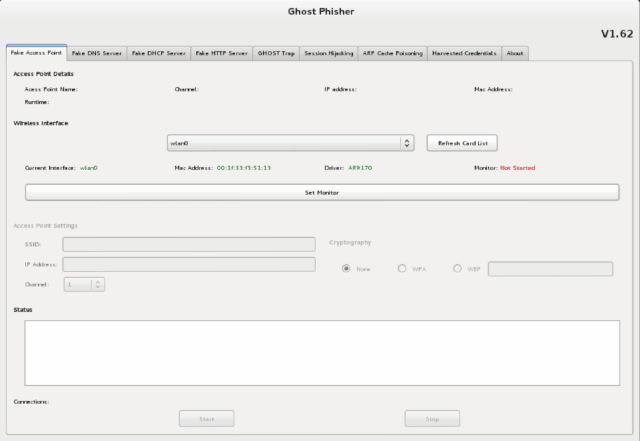
The tool comes with a fake DNS server, fake DHCP server, fake HTTP server and also has an integrated area for automatic capture and logging of HTTP form method credentials to a database. It could be used as a honey pot and could be used to service DHCP requests, DNS requests or phishing attacks.
Ghost Phisher Features
- HTTP Server
- Inbuilt RFC 1035 DNS Server
- Inbuilt RFC 2131 DHCP Server
- Webpage Hosting and Credential Logger (Phishing)
- Wifi Access point Emulator
- Session Hijacking (Passive and Ethernet Modes)
- ARP Cache Poisoning (MITM and DOS Attacks)
- Penetration using Metasploit Bindings
- Automatic credential logging using SQlite Database
- Update Support
Prerequisites
The Program requires the following to run properly:
The following dependencies can be installed using the Debian package installer command on Debian based systems using “apt-get install program” or otherwise downloaded and installed manually.
- Aircrack-NG
- Python-Scapy
- Python Qt4
- Python
- Subversion
- Xterm
- Metasploit Framework (Optional)
You can download Ghost Phisher here:
Or you can read more here.
