dork-cli is a Python-based command-line Google Dork Tool to perform searches against Google’s custom search engine. A command-line option is always good as it allows you to script it in as part of your automated pen-testing suite.
It will return a list of all the unique page results it finds, optionally filtered by a set of dynamic page extensions.
Any number of additional query terms/dorks can be specified. dork-cli was designed to be piped into an external tool such as a vulnerability scanner for automated testing purposes.
Setup dork-cli Google Dork Tool
In order to use this program you need to configure at a minimum two settings: a Google API key and a custom search engine id.
Custom Search Engine:
- Create a custom search engine via https://www.google.com/cse/
- Add your desired domain(s) under “Sites to search”
- Click “Search engine ID” button to reveal the id, or grab it from the “cx” url paramter
API key:
- Open the Google API console at https://code.google.com/apis/console
- Enable the Custom Search API via APIs & auth > APIs
- Create a new API key via APIs & auth > Credentials > Create new Key
- Select “Browser key”, leave HTTP Referer blank and click Create
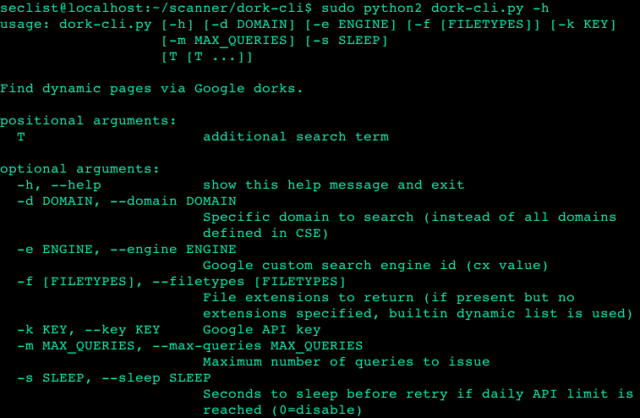
Usage of dork-cli Google Dorking Tool
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 |
$ ./dork-cli.py -h usage: dork-cli.py [-h] [-e ENGINE] [-f [FILETYPES]] [-k KEY] [-m MAX_QUERIES] [-s SLEEP] [T [T ...]] Find dynamic pages via Google dorks. positional arguments: T additional search term optional arguments: -h, --help show this help message and exit -e ENGINE, --engine ENGINE Google custom search engine id (cx value) -f [FILETYPES], --filetypes [FILETYPES] File extensions to return (if present but no extensions specified, builtin dynamic list is used) -k KEY, --key KEY Google API key -m MAX_QUERIES, --max-queries MAX_QUERIES Maximum number of queries to issue -s SLEEP, --sleep SLEEP Seconds to sleep before retry if daily API limit is reached (0=disable) |
API Limitations For Google Dorks
The free Google API limits you to 100 searches per day, with a maximum of 10 results per search. This means if you configure dork-cli.py to return 100 results, it will issue 10 queries (1/10th of your daily limit) each time it is run. You have the option to pay for additional searches via the Google API console. At the time of writing, signing up for billing on the Google API site gets you $300 free to spend on API calls for 60 days.
You can also check out:
– snitch – Information Gathering Tool Via Dorks
– Goolag – GUI Tool for Google Hacking
You can download dork-cli Google Dorks Tool here:
Or read more here.
