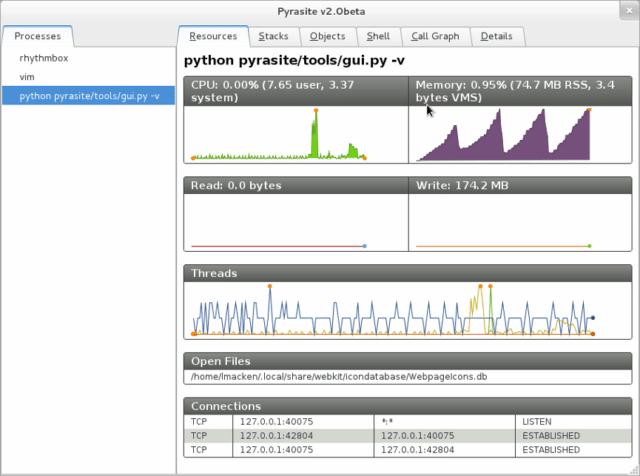
pyrasite is a Python-based toolkit to inject code into running Python processes.
pyrasite works with Python 2.4 and newer. Injection works between versions as well, so you can run Pyrasite under Python 3 and inject into 2, and vice versa.
Usage
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 |
usage: pyrasite [-h] [--gdb-prefix GDB_PREFIX] [--verbose] [--output OUTPUT_TYPE] pid [filepath|payloadname] pyrasite --list-payloads pyrasite - inject code into a running python process positional arguments: pid The ID of the process to inject code into filepath|payloadname The second argument must be a path to a file that will be sent as a payload to the target process or it must be the name of an existing payload (see --list-payloads). optional arguments: -h, --help show this help message and exit --gdb-prefix GDB_PREFIX GDB prefix (if specified during installation) --verbose Verbose mode --output OUTPUT_TYPE This option controls where the output from the executed payload will be printed. If the value is 'procstreams' (the default) then the output is sent to the stdout/stderr of the process. If the value is 'localterm' then the output is piped back and printed on the local terminal where pyrasite is being run. --list-payloads List payloads that are delivered by pyrasite For updates, visit https://github.com/lmacken/pyrasite |
You can download pyrasite here:
Or read more here.
