Maltrail is a malicious traffic detection system, utilizing publicly available (black)lists containing malicious and/or generally suspicious trails, along with static trails compiled from various AV reports and custom user-defined lists, where trail can be anything from domain name (e.g. zvpprsensinaix.com for Banjori malware), URL (e.g. http://109.162.38.120/harsh02.exe for known malicious executable), IP address (e.g. 185.130.5.231 for known attacker) or HTTP User-Agent header value (e.g. sqlmap for automatic SQL injection and database takeover tool).
Also, it uses (optional) advanced heuristic mechanisms that can help in the discovery of unknown threats (e.g. new malware).
Features
- Uses multiple public blacklists (alientvault, autoshun, badips, sblam etc)
- Has extensive static trails for identification (domain names, URLs, IP addresses or User-Agent values)
- Optional heuristic mechanisms for detection of unknown threats
- Based on Traffic -> Sensor <-> Server <-> Client Architecture
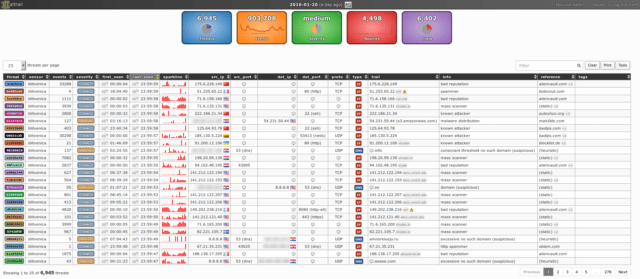
- Web reporting interface
Installation
|
1 2 3 4 |
sudo apt-get install git python-pcapy git clone https://github.com/stamparm/maltrail.git cd maltrail sudo python sensor.py |
You can download maltrail here:
Or read more here.
