sheep-wolf is a tool to help you Exploit MD5 Collisions in software, specially malware samples which are commonly detected using MD5 hash signatures.
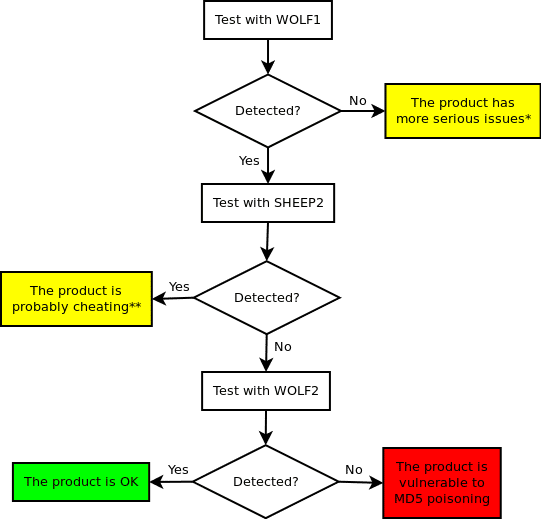 and then a malicious one (Wolf) that have the same MD5 hash. Please use this code to test if the security products in your reach use MD5 internally to fingerprint binaries and share your results by issuing a pull request updating the contents of
and then a malicious one (Wolf) that have the same MD5 hash. Please use this code to test if the security products in your reach use MD5 internally to fingerprint binaries and share your results by issuing a pull request updating the contents of results/!
Dependencies
- 32-bit Windows (virtual) machine (64-bit breaks stuff)
- Visual Studio 2012 to compile the projects (Express will do)
- Fastcoll for collisions
- Optional: Cygwin+MinGW to compile Evilize
How does it work?
shepherd.batexecutesshepherd.exewith the user supplied command line argumentsshepher.exegenerates a header file (sc.h) that contains the encrypted shellcode, the password and the CRC of the plain shellcode
shepherd.batexecutes the build process ofsheep.exesheep.exeis built withsc.hincluded by Visual Studio
shepherd.batexecutesevilize.exeevilize.execalculates a special IV for the chunk ofsheep.exeright before the block where the collision will happenevilize.exeexecutesfastcoll.exewith the IV as a parameterfastcoll.exegenerates two 128 byte colliding blocks:aandb
evilize.exereplaces the original string buffers ofsheep.exeso that they contain combinationsaandb- The resulting files (
evilize/wolf.exeandevilize/sheep.exe) have the same MD5 hashes but behave differently. The real code to be executed only appears in the memory ofevilize/wolf.exe.
You can download sheep-wolf here:
Or read more here.
