pemcracker is a tool for cracking PEM files that are encrypted and have a password. The purpose is to attempt to recover the password for encrypted PEM files while utilising all the CPU cores.
Inspired by Robert Graham’s pemcrack, it still uses high-level OpenSSL calls in order to guess the password. As an optimisation, instead of continually checking against the PEM on disk, it is loaded into memory in each thread.
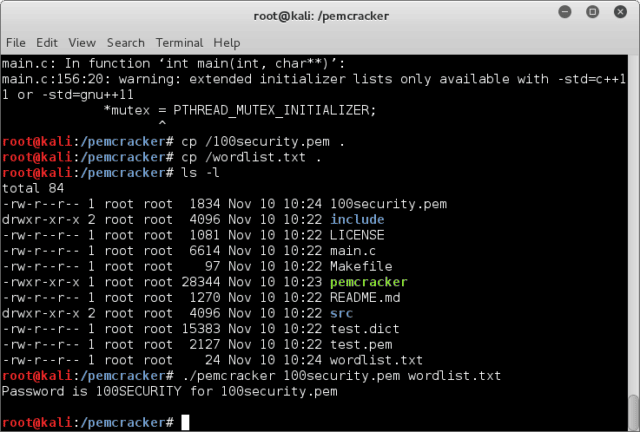
Usage
|
1 2 3 4 5 |
bwall@ragnarok:~$ ./pemcracker pemcracker 0.1.0 pemcracker <path to pem> <word file> pemcracker 0.1.0 by Brian Wallace (@botnet_hunter) |
Example:
|
1 2 |
bwall@ragnarok:~/data/publicprojects/pemcracker$ ./pemcracker test.pem test.dict Password is komodia for test.pem |
If you are looking for the fastest possible method of brute forcing PEM files, you may wish to try out John the Ripper. Its little known ssh2john allows for converting PEM files to a format that can be fed into ./john.
You can download pemcracker here:
Or read more here.
