Kautilya is a human interface device hacking toolkit which provides various payloads for HIDs which may help with breaking into a computer during penetration tests.
The Windows payloads and modules are written mostly in powershell (in combination with native commands) and are tested on Windows 7 and Windows 8. In principal Kautilya should work with any HID capable of acting as a keyboard. Kautilya has been tested on Teensy++ 2.0 and Teensy 3.0 from pjrc.com.
Payloads Available
Windows
- Gather
- Gather Information
- Hashdump and Exfiltrate
- Keylog and Exfiltrate
- Sniffer
- WLAN keys dump
- Get Target Credentials
- Dump LSA Secrets
- Dump passwords in plain
- Copy SAM
- Dump Process Memory
- Dump Windows Vault Credentials
- Execute
- Download and Execute
- Connect to Hotspot and Execute code
- Code Execution using Powershell
- Code Execution using DNS TXT queries
- Download and Execute PowerShell Script
- Execute ShellCode
- Reverse TCP Shell
- Backdoor
- Sethc and Utilman backdoor
- Time based payload execution
- HTTP backdoor
- DNS TXT Backdoor
- Wireless Rogue AP
- Tracking Target Connectivity
- Gupt Backdoor
- Escalate
- Remove Update
- Forceful Browsing
- Manage
- Add an admin user
- Change the default DNS server
- Edit the hosts file
- Add a user and Enable RDP
- Add a user and Enable Telnet
- Add a user and Enable Powershell Remoting
- Drop Files
- Drop a MS Word File
- Drop a MS Excel File
- Drop a CHM (Compiled HTML Help) file
- Drop a Shortcut (.LNK) file
- Drop a JAR file
Misc
- Browse and Accept Java Signed Applet
- Speak on Target
Linux
- Download and Execute
- Reverse Shells using built in tools
- Code Execution
- DNS TXT Code Execution
- Perl reverse shell (MSF)
OSX
- Download and Execute
- DNS TXT Code Execution
- Perl Reverse Shell (MSF)
- Ruby Reverse Shell (MSF)
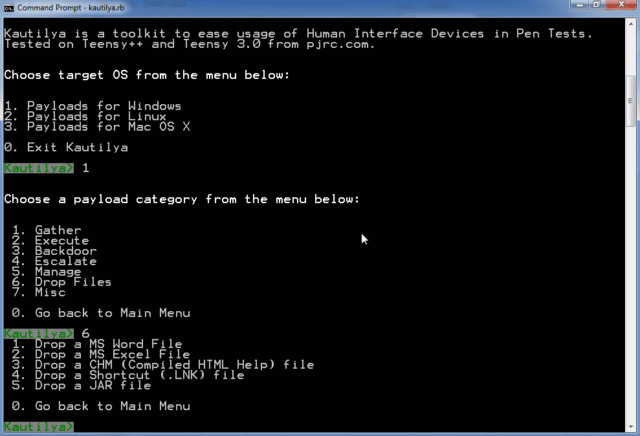
Usage
Run kautilya.rb and follow the menus. Kautilya asks for your inputs for various options. The generated payload is copied to the output directory of Kautilya.
The generated payload is an arduino sketch, ready to be used with Arduino IDE. Burn it to Human Interface Device of your choice and have fun!
You can download Kautilya here:
Or read more here.
