Today let’s talk about securing MySQL installation on Ubuntu, in this case specifically Ubuntu 16.04 LTS which was released not too long ago.
So I love Ubuntu and I use it for everything, especially the LTS (Long Term Support) releases for servers. MySQL is not my best buddy, but a necessary evil many times – like this blog as I still do love WordPress.
If you’re going to use them together, you better learn how to secure your installation properly to avoid getting into a nasty situation like Yahoo did recently.
This guide from Acunetix goes way more in depth than your average “install from the package manager, use a good password etc” kinda guide, so if you wanna go to the next level on securing your setup you are going to want to check this out.
In this series, we will focus on how to create a more secure environment for MySQL server, which is currently the second most popular database management system (DBMS), in order to prevent common attacks, as well as to mitigate the attack vector of other vulnerabilities.
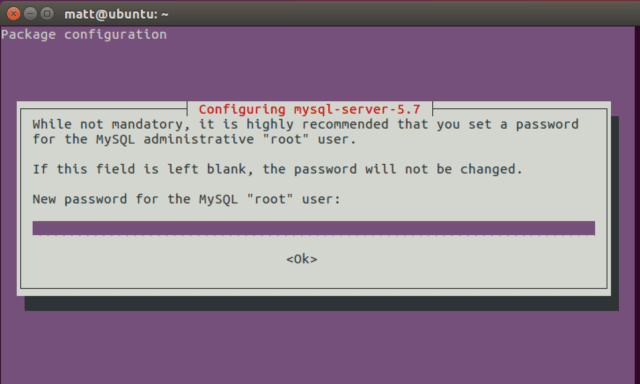
For the purposes of this article we have setup a machine running Ubuntu 16.04 LTS (Xenial Xerus) and MySQL 5.7. We have also edited our hosts file to point ‘example.com’ to the IP address of our test machine.
The guide runs all the way through the process covering:
– Installing MySQL
– MySQL Setup
– Testing Installation
– Configuring MySQL Securely
– Logs
– Backups
– Updates
– SQL Injection Impact
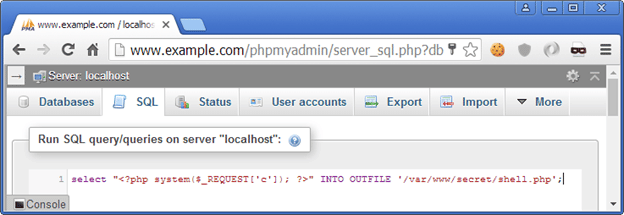
Throughout this series, we have analyzed how various configuration options can affect our MySQL installation security, and how, as demonstrated in the sample attack scenario, a simple SQL injection vulnerability in combination with a misconfigured server can have devastating results–everything from database enumeration, unauthorized access, secret files to potential server compromise.
Read the full guide here: Securing MySQL Server on Ubuntu 16.04 LTS
