So the Linode DDoS attack – seems like this xmas has been a terrible time for sys admins, along with what happened to Steam and A Small Orange (100+ hours down).
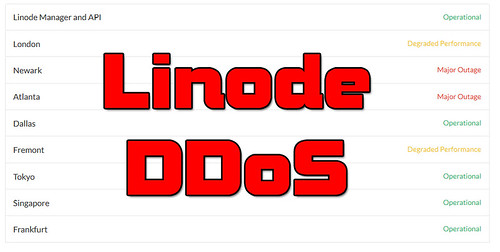
A whole lot of work during the most drunken holiday of the year, not fun. And yes it affected me too, work wise everything is hosted on Linode – and this site is also hosted on Linode. So I got spammed with SMS alerts from Dec 26th – Dec 28th (thankfully not on xmas day itself). The above image is actually my own screenshot I sent to the team to update everyone on the situation on boxing day.
And the attacks are still ongoing to some degree as you can see on the Linode status page here: http://status.linode.com/
Virtual server host Linode has been on and offline since Christmas Day as it weathers an ongoing denial-of-service attack. Four days in, its customers are getting grumpy.
LinodeStatus page … Linode still suffering days after attacks began
“We are currently aware of a DoS attack that is affecting the Linode Manager/Website and our Dallas datacenter. This post will be updated as soon as we have more information to provide,” the biz said in the wee small hours of Christmas Day.
While billions settled in for the end-of-year festivities, floods of network traffic overwhelmed Linode’s systems in Dallas, Texas, and took parts of its website down. By 3am on the 26th, the waves of packets seemed to be dying down, but then the attackers shifted their sights to the company’s other data centers.
People were getting antsy all over and moving to other hosts like Digital Ocean, RamNode and Vultr.
Can’t blame them really, even if you had a hot fail-over in a different Linode DC – you’d likely still be affected.
Later that day, Linode’s data centers in Atlanta, Georgia, and Newark, New Jersey, took hits – as did the company’s London hosting center. The assailants then started hammering the Dallas data center again, effectively knocking people’s virtual servers offline.
Atlanta, Newark, and London were brought back online a day later, although the two US data centers, plus a third in Fremont, California, were soon floored again. Now it seems only the Dallas site is under attack, causing “degraded performance,” according to Linode.
Punters have been venting about the situation, with the linuxadmin and webdev subreddits getting complaints. With little more than stock statements coming out of Linode, some users are threatening to move to rival services, such as Vultr and DigitalOcean.
A spokesperson for Linode was not available for comment.
It seems like the attack is still being aimed at their biggest DC, which is Dallas and the home of the Linode site and manager. This means the Linode Manager, API and the Dallas DC itself are still suffering degraded performance – but are not totally offline.
The DDoS seems to be quite a broad, powerful attack against the entire Linode infrastructure – targeting various bits which can degrade an entire data centre and moving the attack upstream as it got blocked.
Source: The Register
